CyberDefenders - CorporateSecrets
Table of Contents
Scenario
A windows forensics challenge prepared by Champlain College Digital Forensics Association for their yearly CTF.
Windows Image Forensics Case created By AccessData® FTK® Imager 4.2.1.4
Acquired using: ADI4.2.1.4
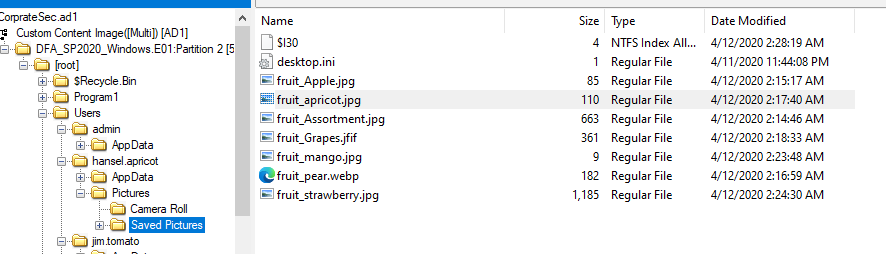
Information for F:\DFAWindows\DFASP2020_Windows:
Physical Evidentiary Item (Source) Information:
- [Device Info]
- Source Type: Physical
- [Drive Geometry]
- Cylinders: 6,527
- Heads: 255
- Sectors per Track: 63
- Bytes per Sector: 512
- Sector Count: 104,857,600
[Physical Drive Information]
- Drive Interface Type: lsilogic [Image]
- Image Type: VMWare Virtual Disk
- Source data size: 51200 MB
- Sector count: 104857600
[Computed Hashes]
- MD5 checksum: e5fe043aa84454237438cdb2b78d08b3
- SHA1 checksum: ada83cd44e294ab840fa7acd77cf77e81c3431b3
Image Information:
- Segment list:
- F:\DFAWindows\DFASP2020Windows.E01
- F:\DFAWindows\DFASP2020Windows.E02
- F:\DFAWindows\DFASP2020Windows.E03
- F:\DFAWindows\DFASP2020Windows.E04
- F:\DFAWindows\DFASP2020Windows.E05
- F:\DFAWindows\DFASP2020Windows.E06
- F:\DFAWindows\DFASP2020Windows.E07
- F:\DFAWindows\DFASP2020Windows.E08
- F:\DFAWindows\DFASP2020_Windows.E09
Your objective as a soc analyst is to analyze the image and answer the question.
Category: Endpoint Forensics
Tools: - FTK Imager - Registry Explorer - RegRipper - HxD - DB Browser for SQLite - HindSight - Event Log Explorer - MFTDump
Questions
Q1: What is the current build number on the system?
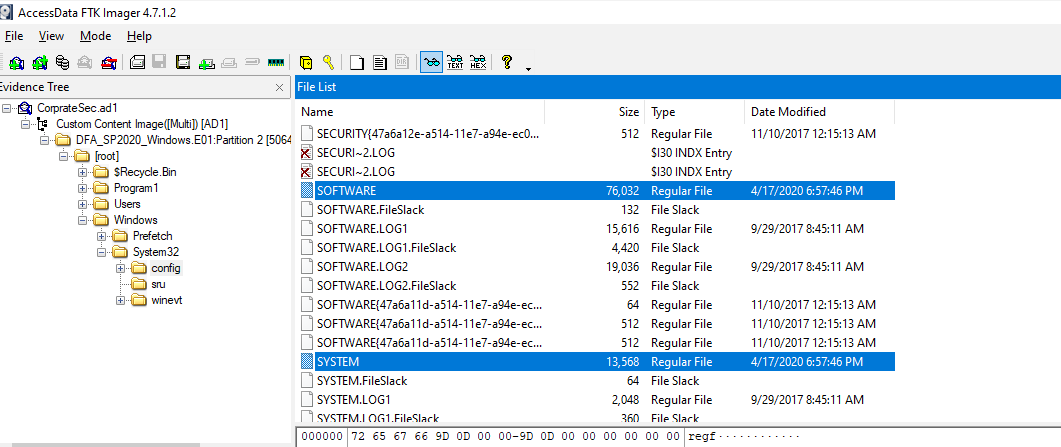
We can get system information from registry hive that located in Windows\System32\config, export all the hive so we don't need to come back later when needed
Use RegRipper or RegistryExplorer then to go SOFTWARE\Microsoft\Windows NT\CurrentVersion which hold this information
16299
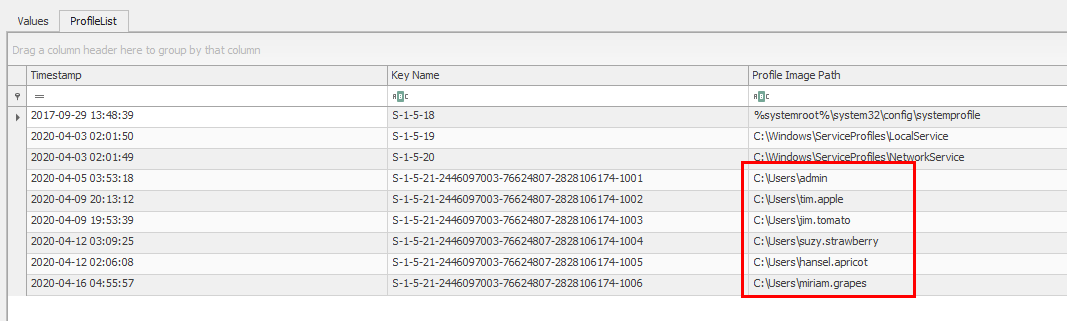
Q2: How many users are there?
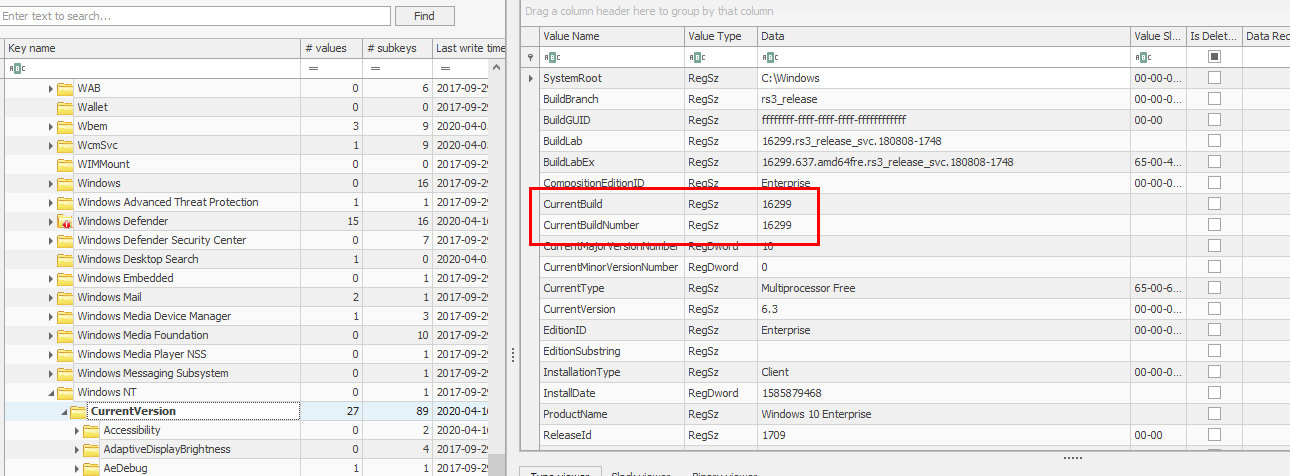
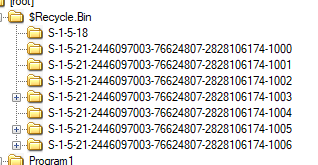
A registry key that hold all SID and profile path of all users inside a system is HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList
Which we can see that there are 6 users on this system
Alternatively, you can see locate to Users folder and count all folders there
6
Q3: What is the CRC64 hash of the file "fruit_apricot.jpg"?
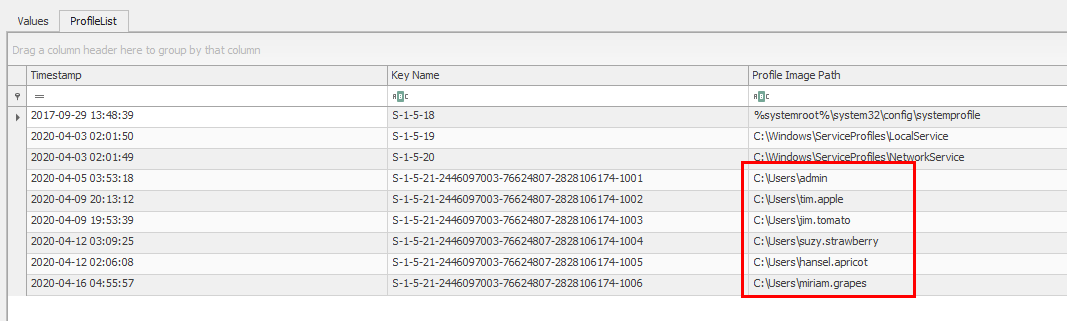
This image is located in hansel.apricot\Pictures\Saved Picture
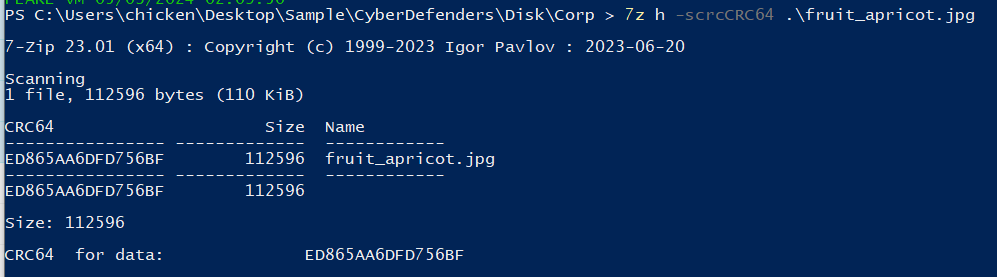
export it and we can use 7z to calculate CRC34 hash for us with this command 7z j -scrcCRC64 fruit_apricot.jpg
- h parameter telling 7z that we're using this program to calculate filehash while we need to pass an algorithm as an argument after then and lastly is the file we will calculate filehash
ED865AA6DFD756BF
Q4: What is the logical size of the file "strawberry.jpg" in bytes?
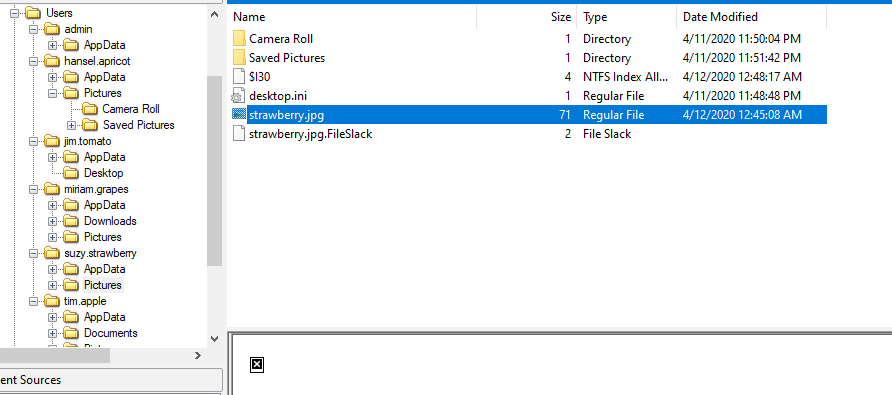
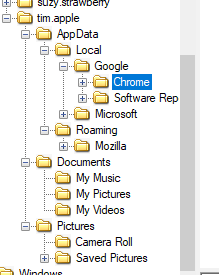
This file located inside suzy.strawberry\Pictures
Export it and we can just use our cmd, powershell and bash to display logical file size
72448
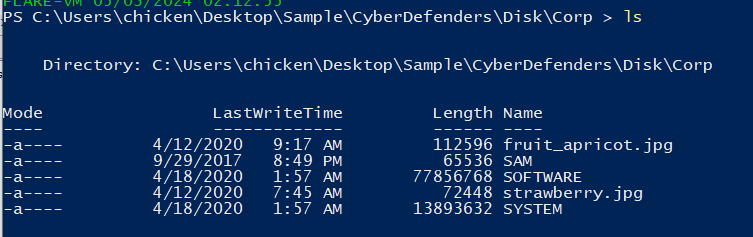
Q5: What is the processor architecture of the system? (one word)
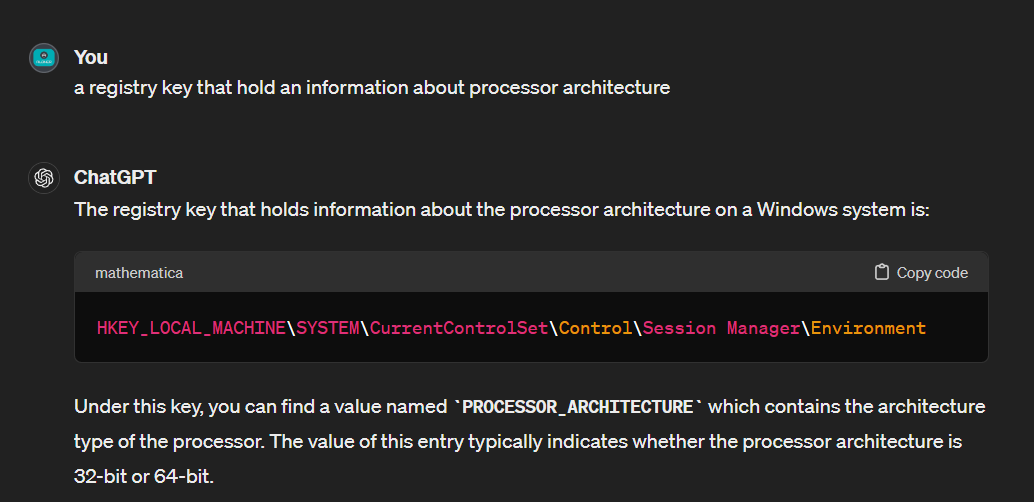
I asked ChatGPT for this question and it told us which registry key we need to get HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Environment
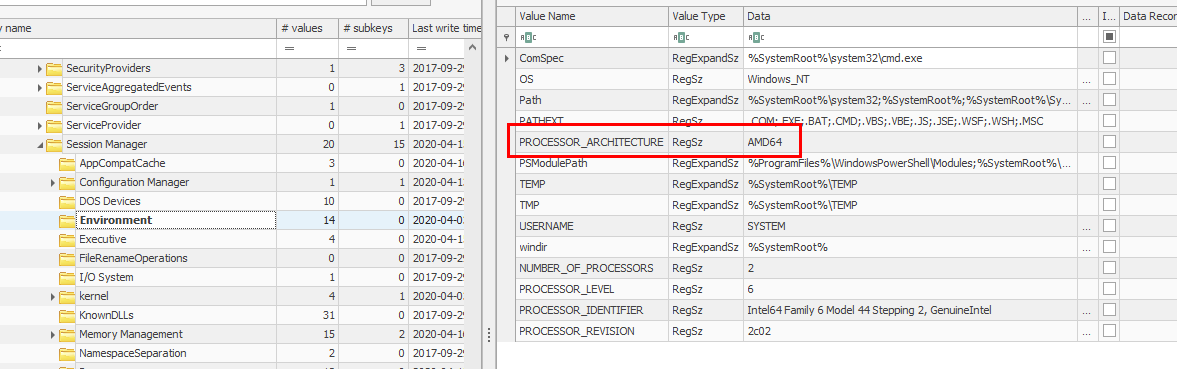
AMD64
Q6: Which user has a photo of a dog in their recycling bin?
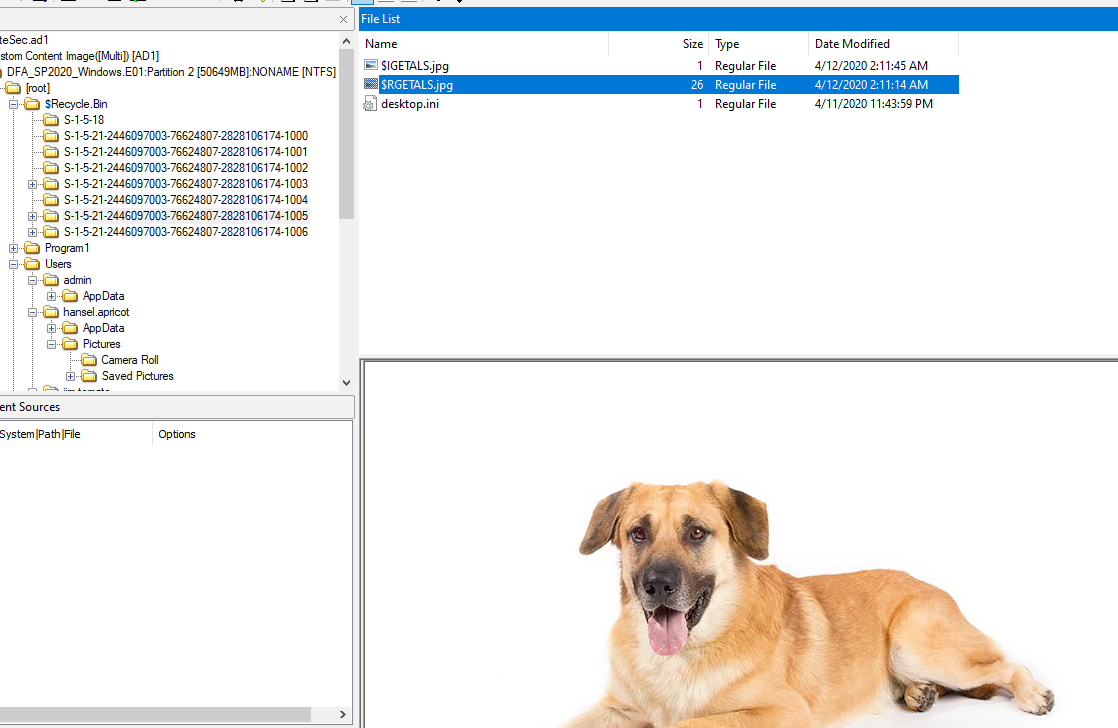
Go to recycle bin and searching through all image files which the only photo of a dog is this image
This image belong to hansel
hansel.apricot
Q7: What type of file is "vegetable"? Provide the extension without a dot.
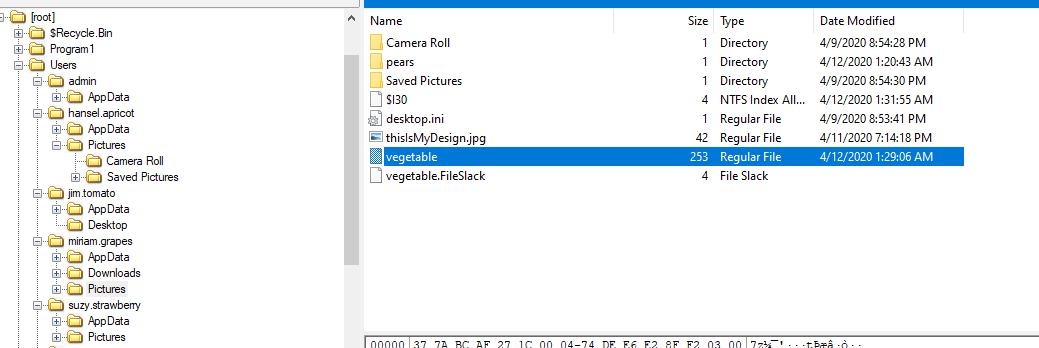
This file was located in miriam.grapes\Pictures
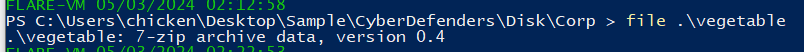
Export it and use file to detect it signature which turn out it's a 7z file
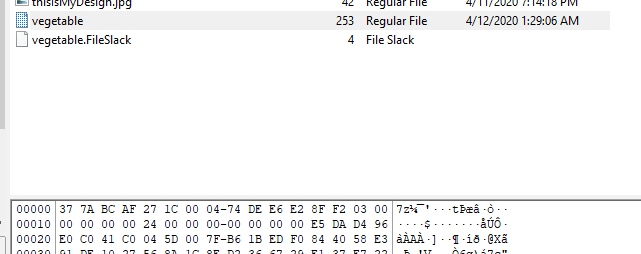
The other way we can solve this question without exporting this file is to look at magic number which totally matched 7z file format (https://en.wikipedia.org/wiki/Listoffile_signatures)
7z
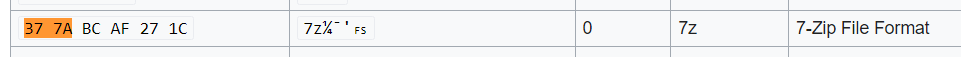
Q8: What type of girls does Miriam Grapes design phones for (Target audience)?
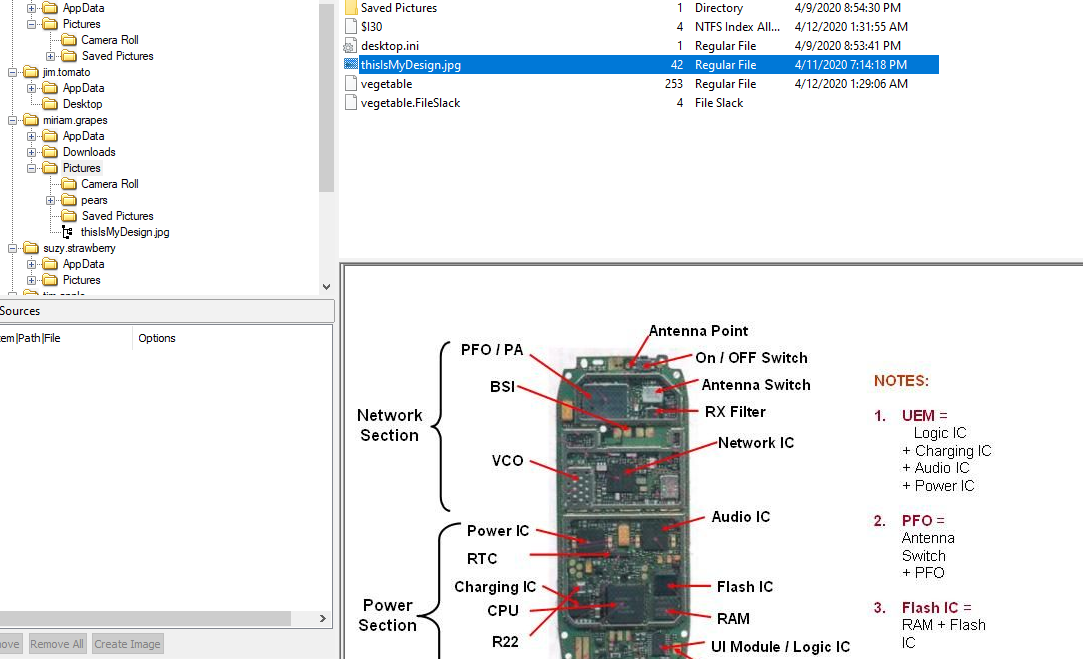
Inside Miriam's Pictures folder, we can see other image file (thisisMyDesign.jpg) which is an image of her design for new phone
When trying to design something for target audience, we need to know our target audience first which research is required which means browser history has riched information when it comes to researching something online
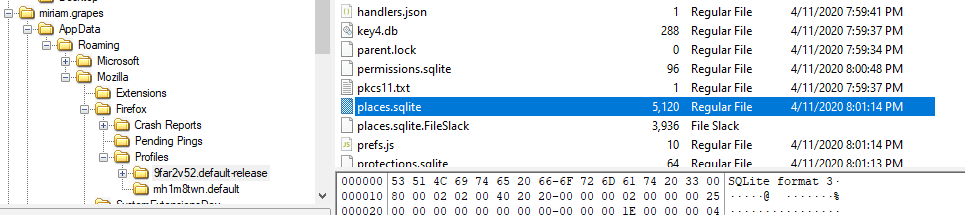
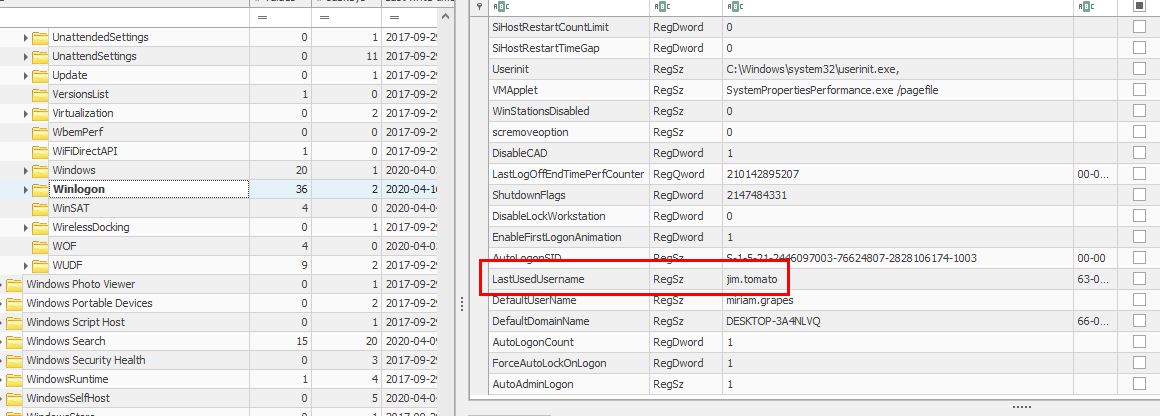
Miriam doesn't have Google folder inside App Data but Mozilla folder is there which mean she's using FireFox as her main browser and we need to export places.sqlite from FireFox profiles folder
Using MZHistoryView or BrowserHistoryView from Nirsoft, we can see that the target audience of this phone is VSCO girl
VSCO
Q9: What is the name of the device?
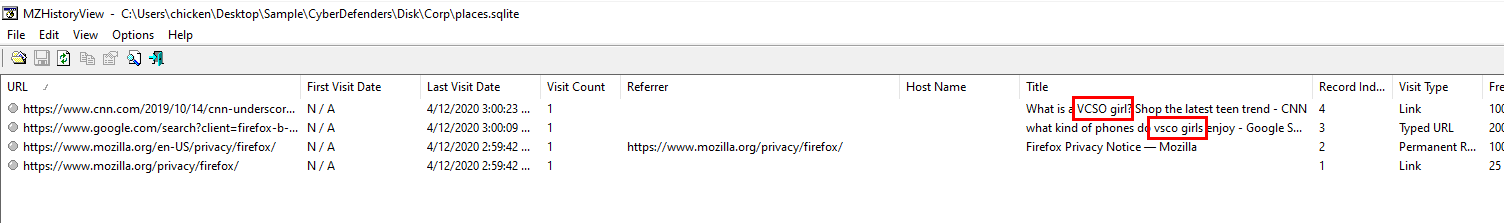
This HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName key hold an information about Computer Name
DESKTOP-3A4NLVQ
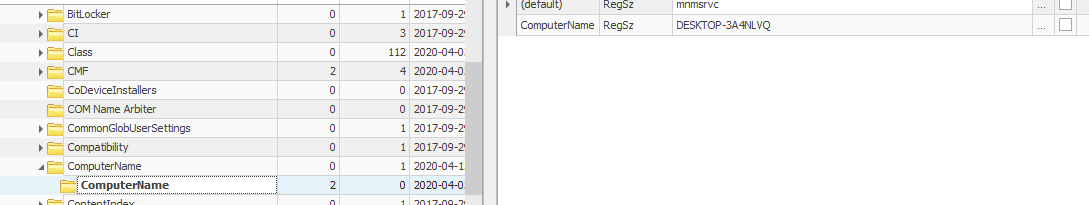
Q10: What is the SID of the machine?
Looking at these bunch of series of number, last 4 digits are SID of each user and the rest is SID of this machine
S-1-5-21-2446097003-76624807-2828106174
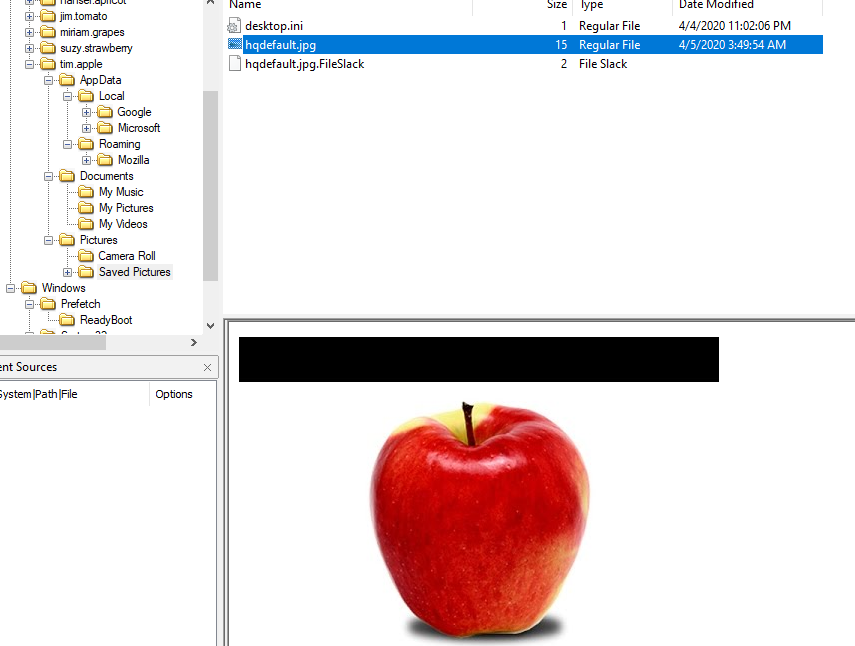
Q11: How many web browsers are present?
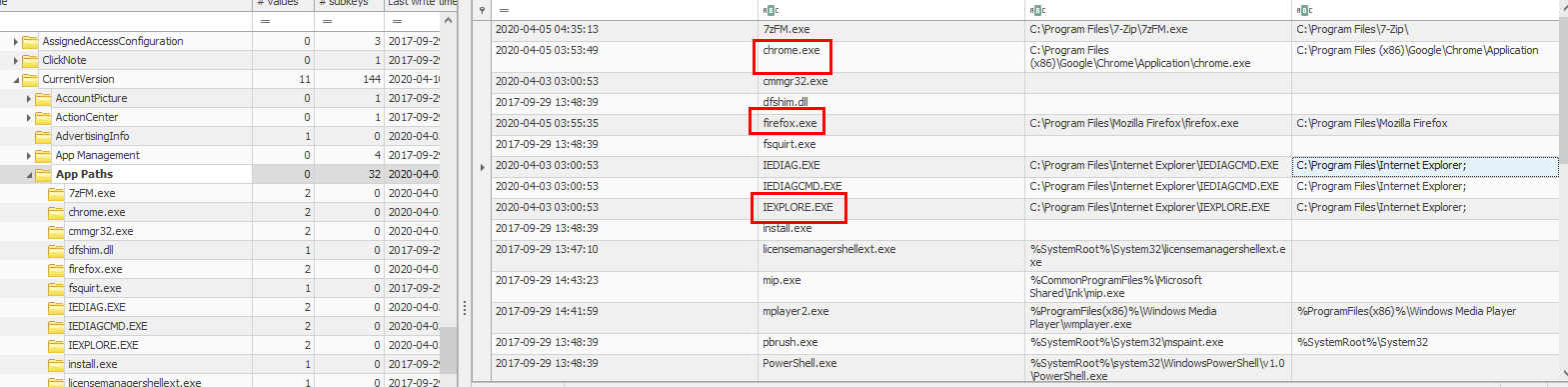
I was too lazy to search for every AppData folders so I went to Software hive and find this HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths registry key that hold path of all (mostly) installed software on this system
We have Chrome, Firefox and Interet Explorer which is obviously came with Edge but look like 4 is not the right answer
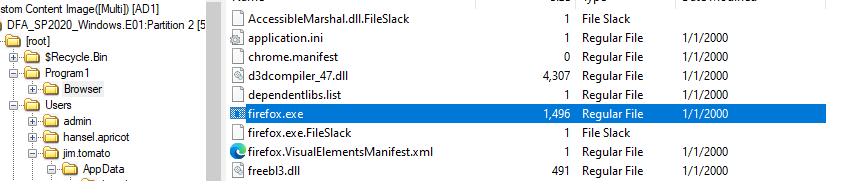
I had to choice but to search for other browser which I found Tor browser shortcut which have weird target as firefox.exe
But in the end, it's a Tor Browser so this system has 5 browsers
5
Q12: How many super secret CEO plans does Tim have? (Dr. Doofenshmirtz Type Beat)
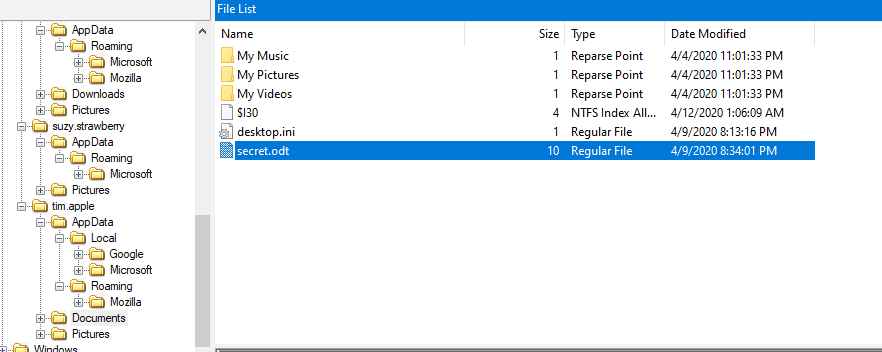
Navigate to tim folder then I located this secret.odt file inside Documents folder
What is this file?, its a file generated by LibreOffice function like doc for Microsoft Word
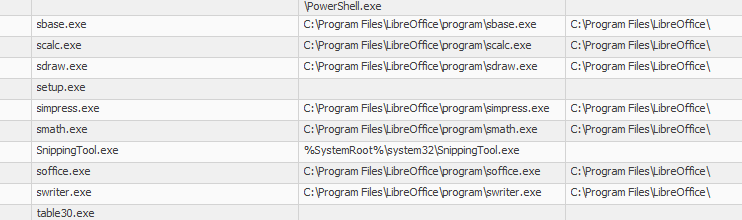
On App Paths registry key, It confirmed that LibreOffice was installed on this system
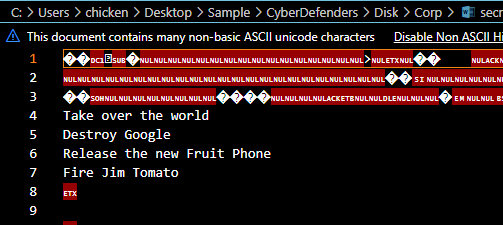
You can export and open it with LibreOffice and the inside of this file holds 4 objectives of Tim
4
Q13: Which employee does Tim plan to fire? (He's Dead, Tim. Enter the full name - two words - space separated)
We know from Tim's secret file that he want to fire Jim
Jim Tomato
Q14: What was the last used username? (I didn't start this conversation, but I'm ending it!)
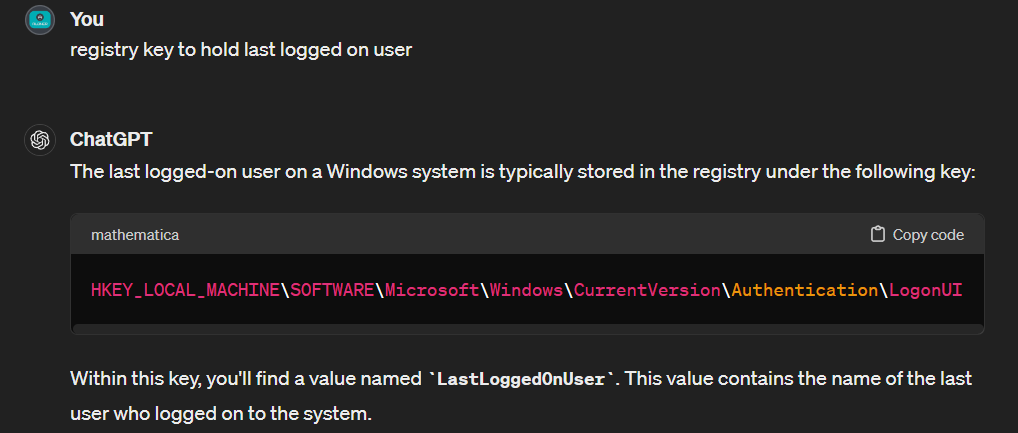
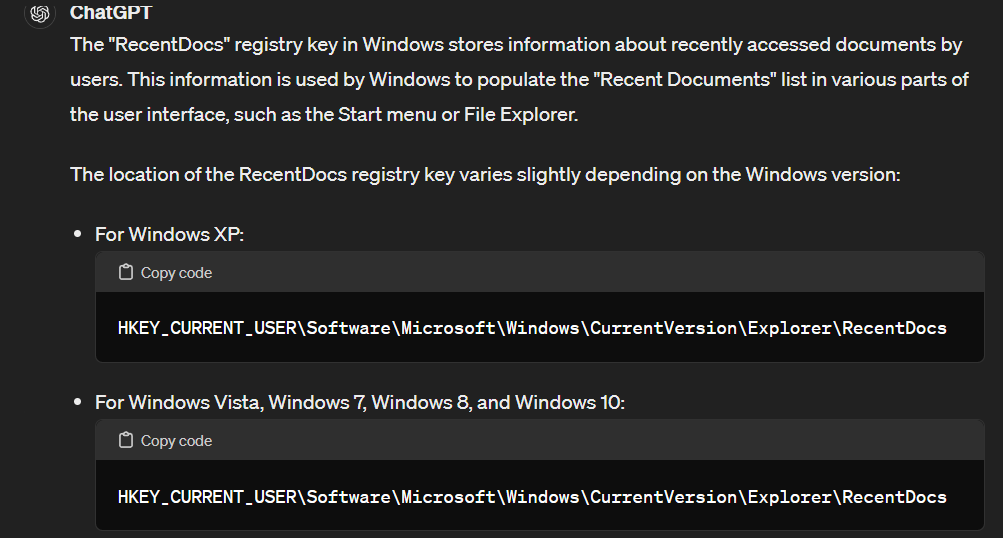
I asked ChatGPT for last logged on username
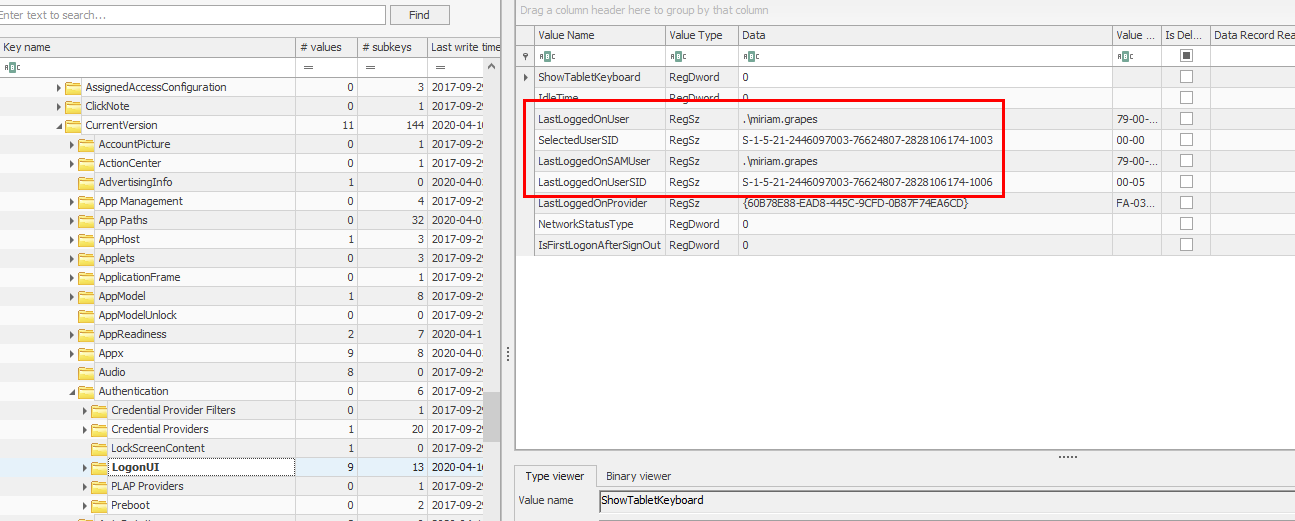
When to this key but turn out this is not the right answer so I did some more research on my own
And went to this SOFTWARE\Microsoft\Windows NT\CurrentVersion\WinLogon key which holds the answer of this question as it hold "LastUsedUsername" not "Last Logged In User" as i thought
jim.tomato
Q15: What was the role of the employee Tim was flirting with?
I tried to search through Tim's folders which I found that Chrome and Firefox history might return something for me so I exported both history file (places.sqlite,History)
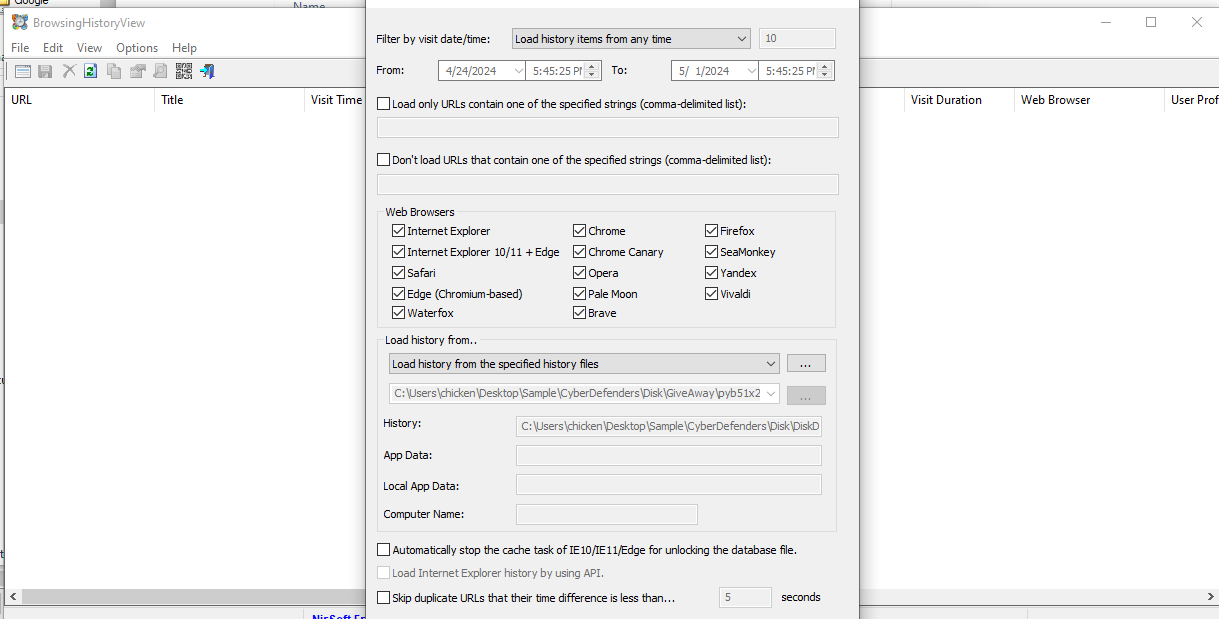
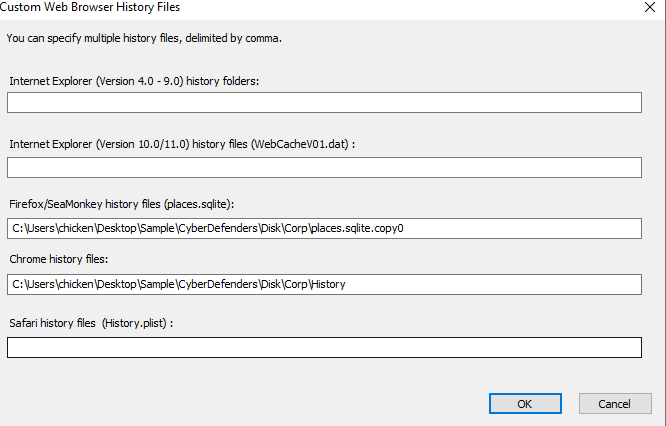
Use BrowserHistoryView from Nirsoft to import both files then display browser of both browsers all at once
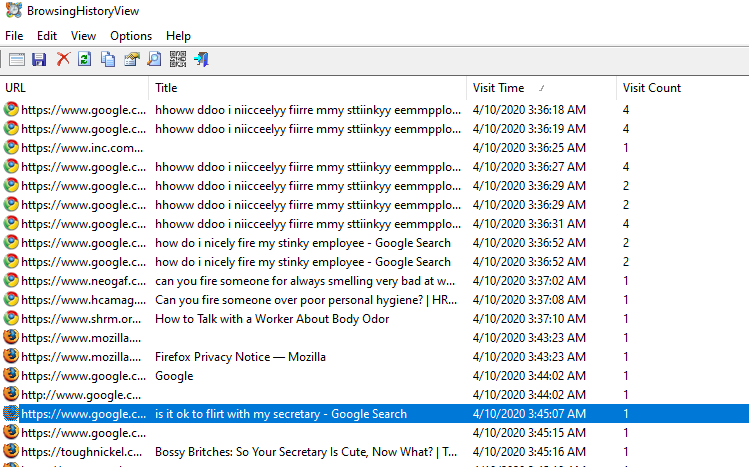
Tim did search Google about it so now we know that secretary is his target
And we also know that he also want to fire some stinky employee based on this browser history
secretary
Q16: What is the SID of the user "suzy.strawberry"?
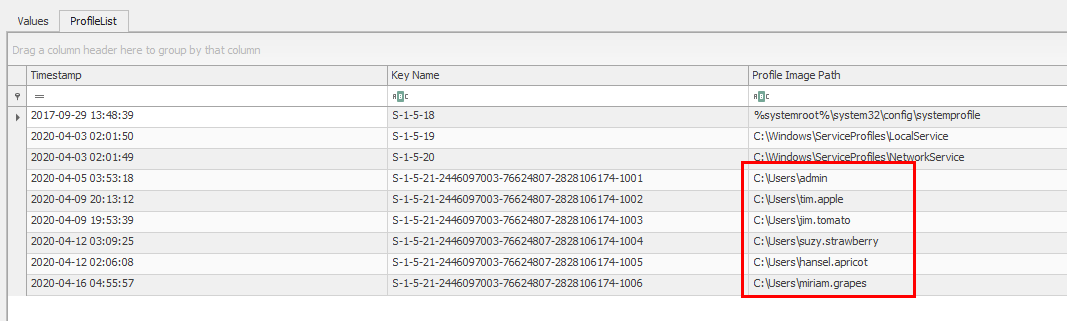
Back to ProfileList registry key, user suzy's SID is 1004
1004
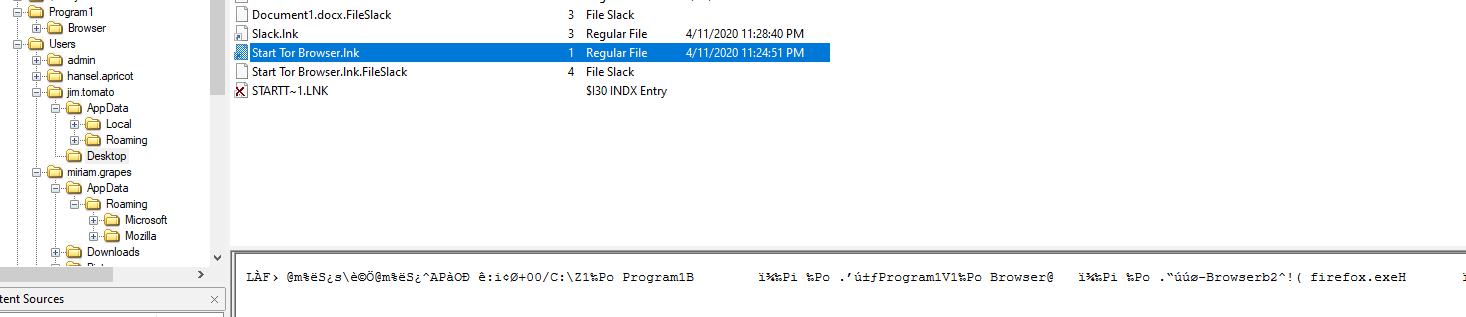
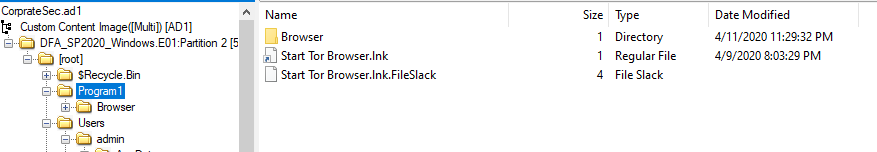
Q17: List the file path for the install location of the Tor Browser.
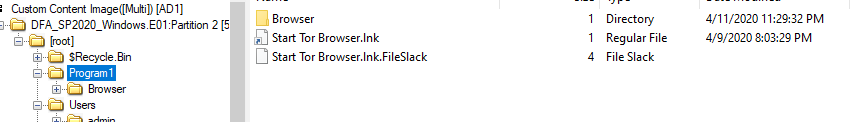
We all know it was installed in \Program1 as the shortcut file guided us through
C:\Program1
Q18: What was the URL for the Youtube video watched by Jim?
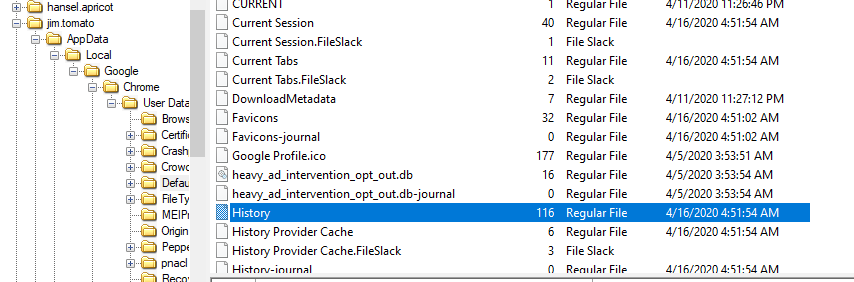
Jim has Chrome installed so lets export history file
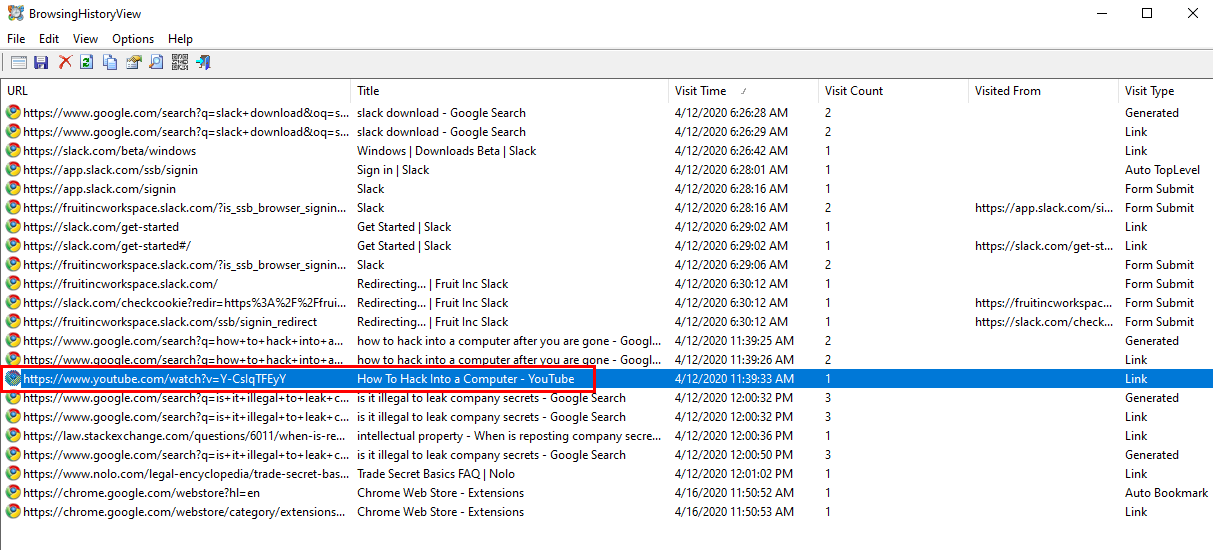
And using our friend from Nirsoft to display them, only Youtube url here is "How to Hack into a Computer" video
https://www.youtube.com/watch?v=Y-CsIqTFEyY
Q19: Which user installed LibreCAD on the system?
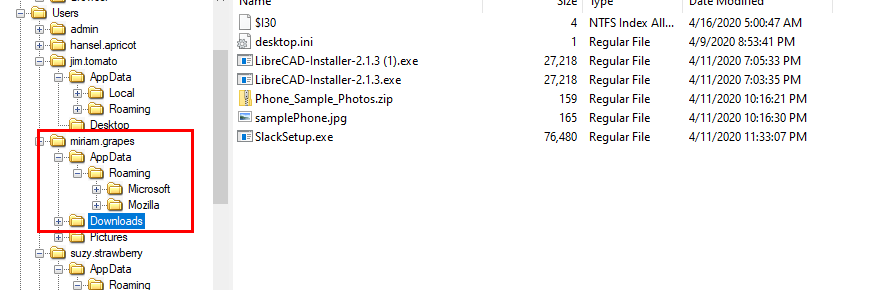
It has to be installer software on any user folder which I found it on Miriam's Downloads folder
miriam.grapes
Q20: How many times "admin" logged into the system?
We can answer this by using Event log or SAM hive and I chose SAM
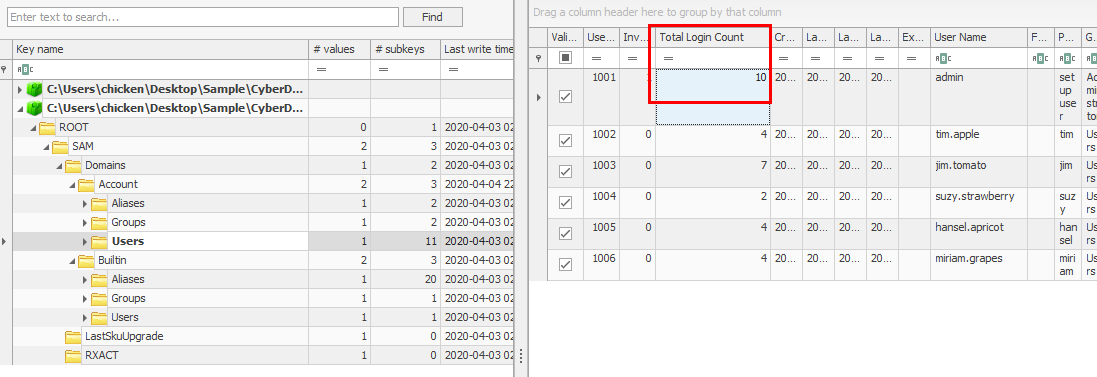
Go to SAM\Domains\Account\Users, we can see that it stores total login count of all users and admin user logged into system 10 times
10
Q21: What is the name of the DHCP domain the device was connected to?
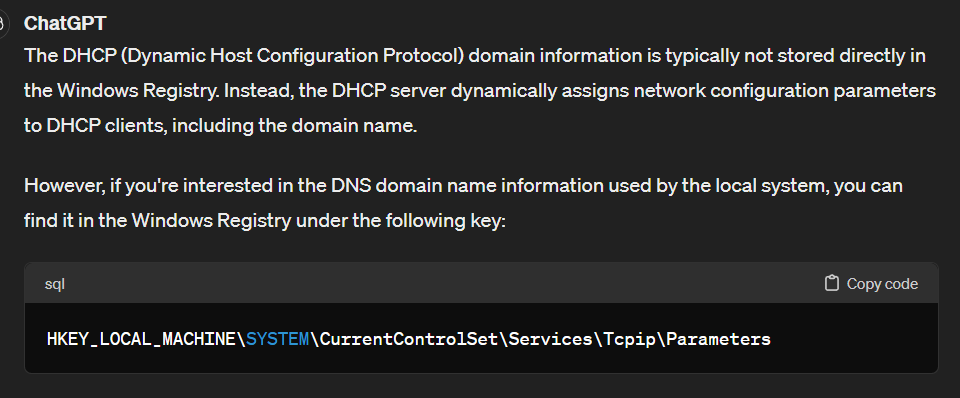
I asked my friend ChatGPT for this question which tell me to get this SYSTEM\ControlSet001\Services\Tcpip\Parameters key
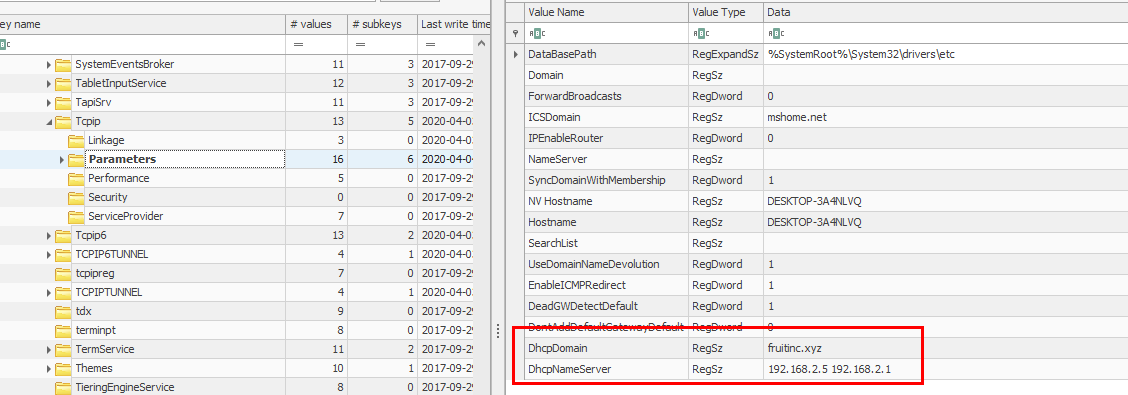
fruitinc.xyz
Q22: What time did Tim download his background image? (Oh Boy 3AM . Answer in MM/DD/YYYY HH:MM format (UTC).)
I asked ChatGPT that if there is a registry key that store a path to background image on Windows which there is one in NTUSER.DAT hive
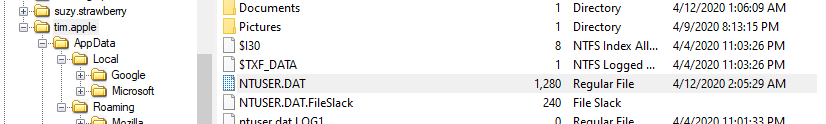
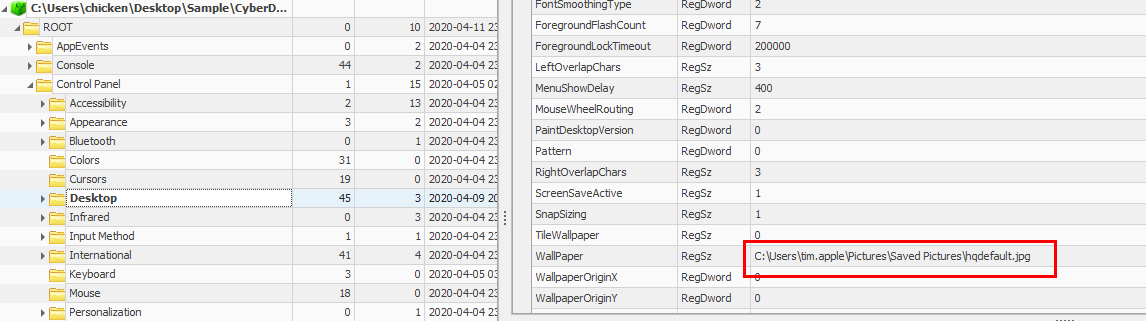
Once we got path to this file, we can navigate to this folder directly
We don't need to use export and use exiftool to analyze this file for us but Date Modified display on FTK Image is enough to answer this question
04/05/2020 03:49
Q23: How many times did Jim launch the Tor Browser?
We know that this Tor Browser executable was renamed to firefox.exe
Which help of TryHackMe Windows Forensic room (Here this the write-up)
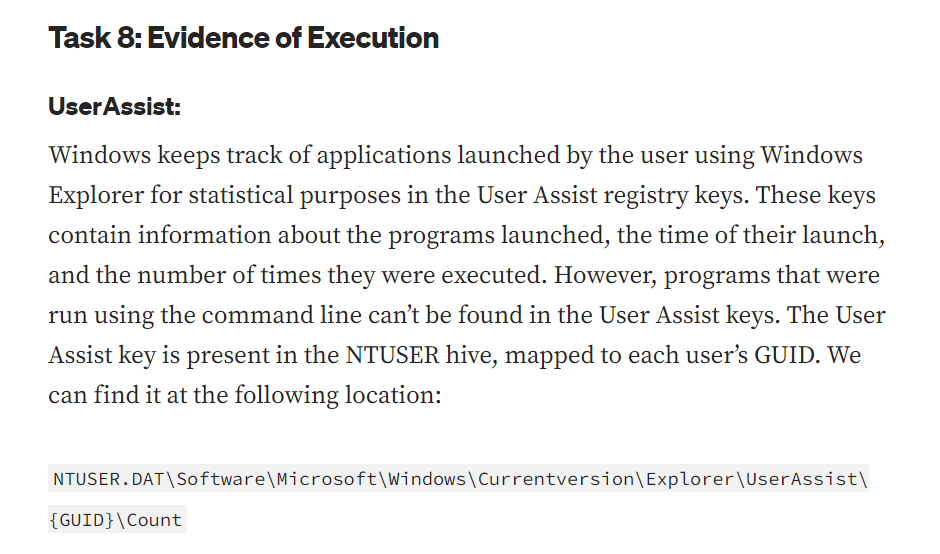
We know where to look for (Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\)
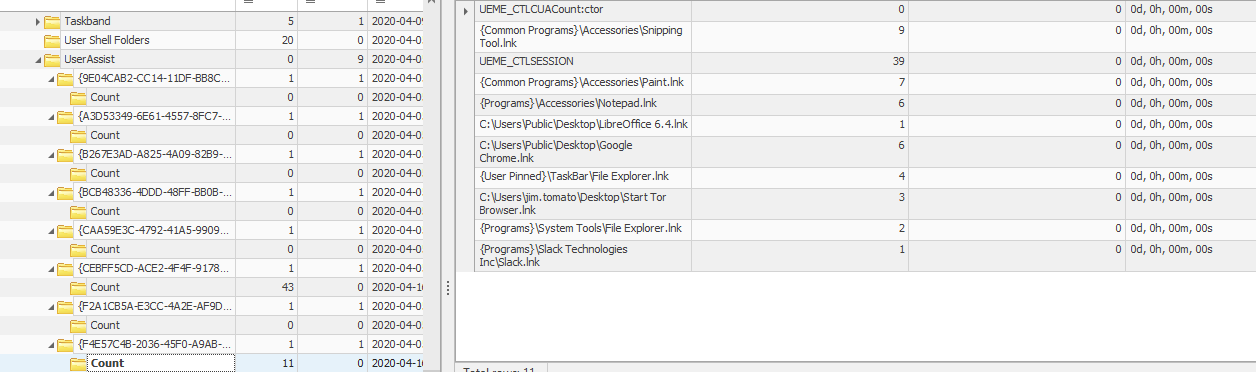
Now its time to find through all GUID to find which one is the right one
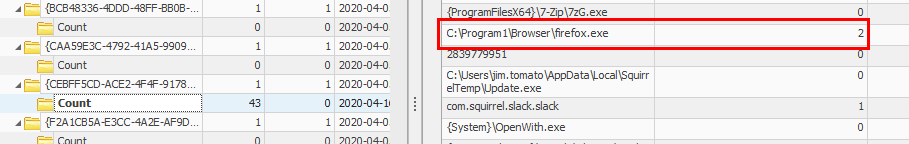
And the only registry key that count firefox.exe is this GUID which was executed Tor 2 times
2
Q24: There is a png photo of an iPhone in Grapes's files. Find it and provide the SHA-1 hash.
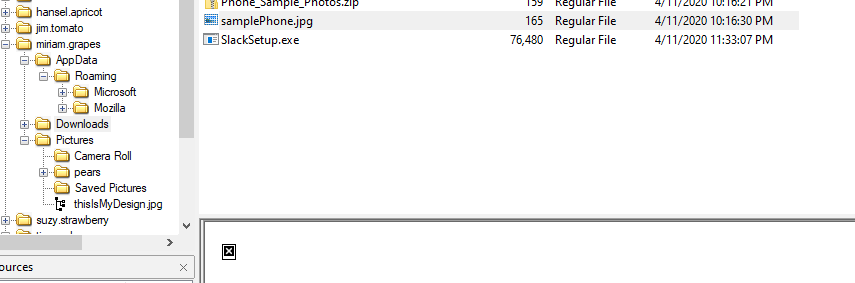
I didn't find any png file but I found this image file on Grapes's Downloads folder and FTK image refused to display this image to me
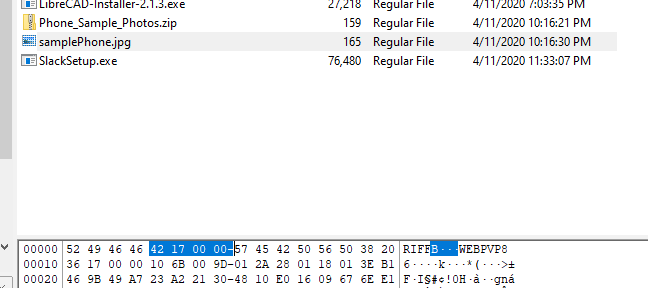
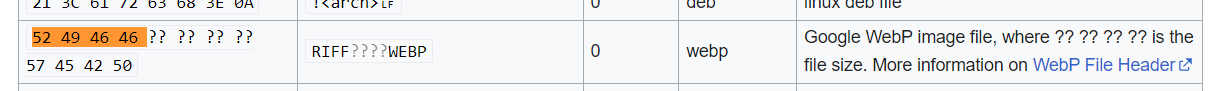
But after checking magic number of this file, turn out it's not a legitimate jpeg file which could be use to hide png file inside of it
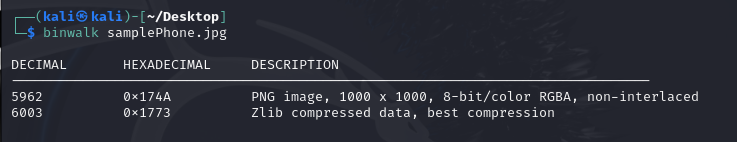
After disappointing from steghide now binwalk is confirming the existence of this PNG file (binwalk samplePhone.jpg)
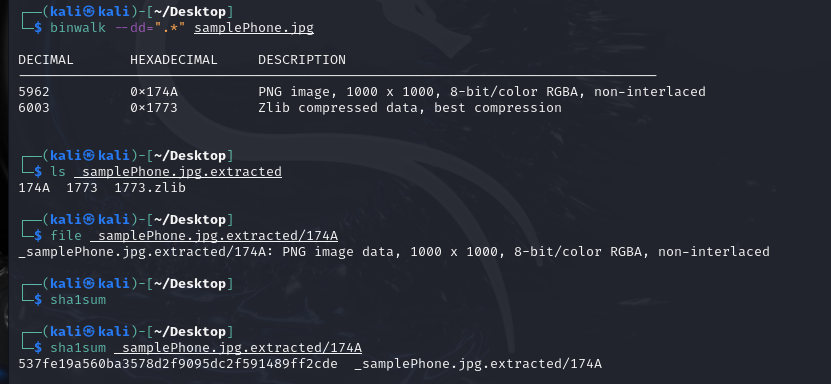
Now use binwalk with --dd to extract any files inside this image
binwalk --dd=".*" samplePhone.jpg
Then use sha1sum to calculate sha1 hash of this png file
sha1sum _samplePhone.jpg.extracted/174A
537fe19a560ba3578d2f9095dc2f591489ff2cde
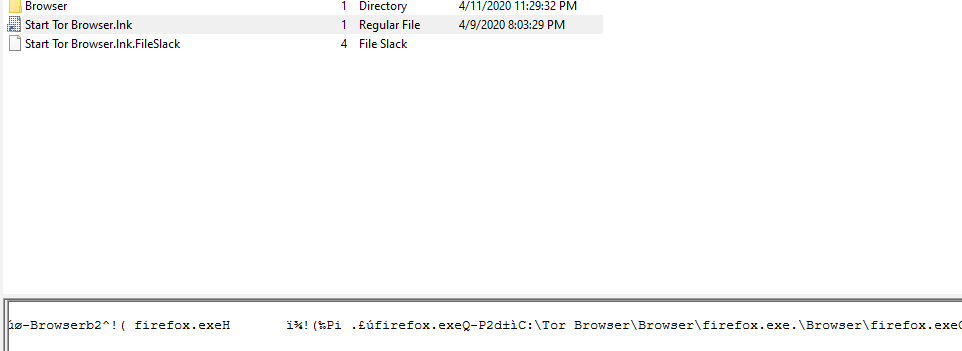
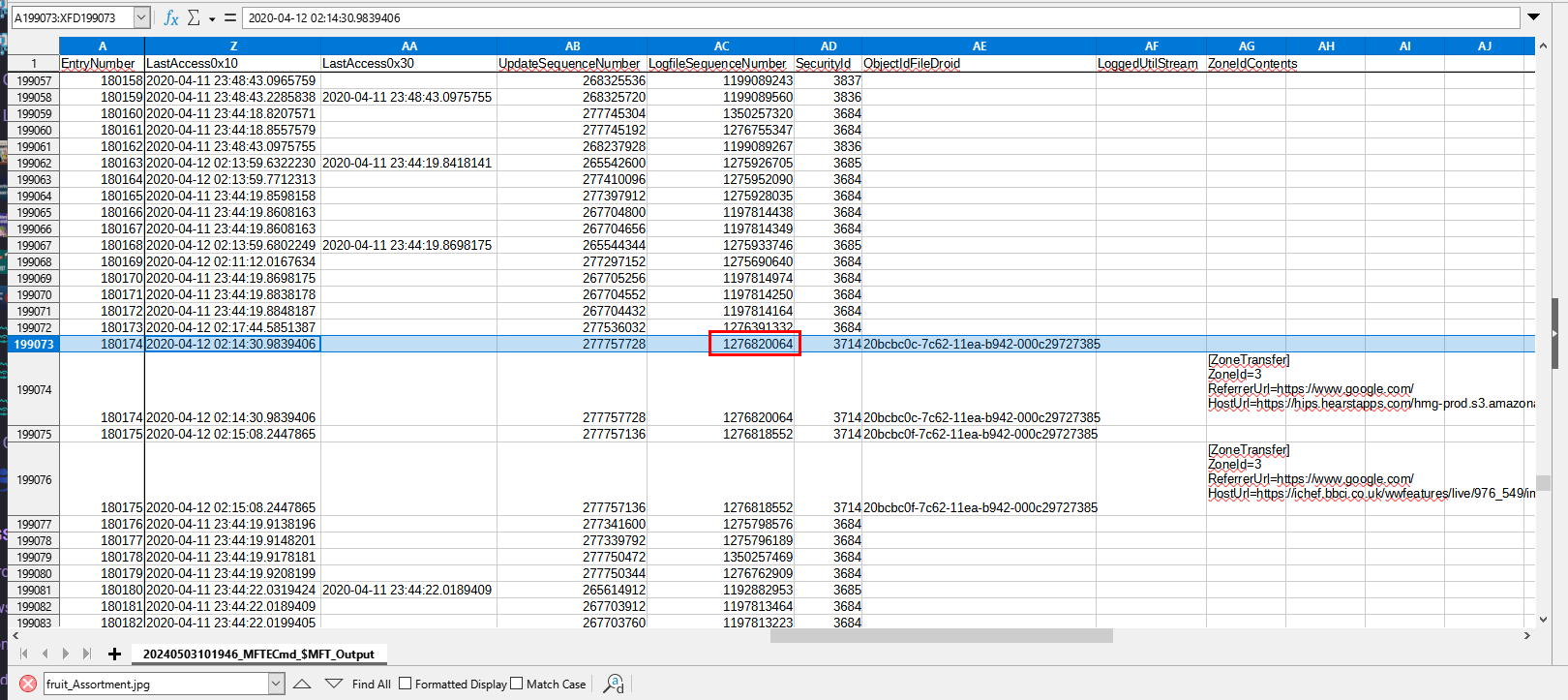
Q25: When was the last time a docx file was opened on the device? (An apple a day keeps the docx away. Answer in UTC, YYYY-MM-DD HH:MM:SS)
My friend told me that RecentDocs registry key could be used for this but we need to get all NTUSER.DAT hives available on this system
I found only 4 users have NTUSER.DAT hive which are
- admin
- jim.tomato
- miriam.graps
- tim.apple
So lets grab all of them and Check out each Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs keys
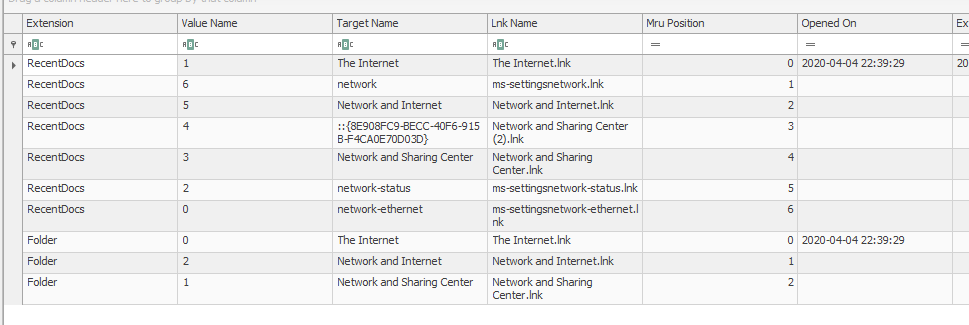
admin didn't open any docx file
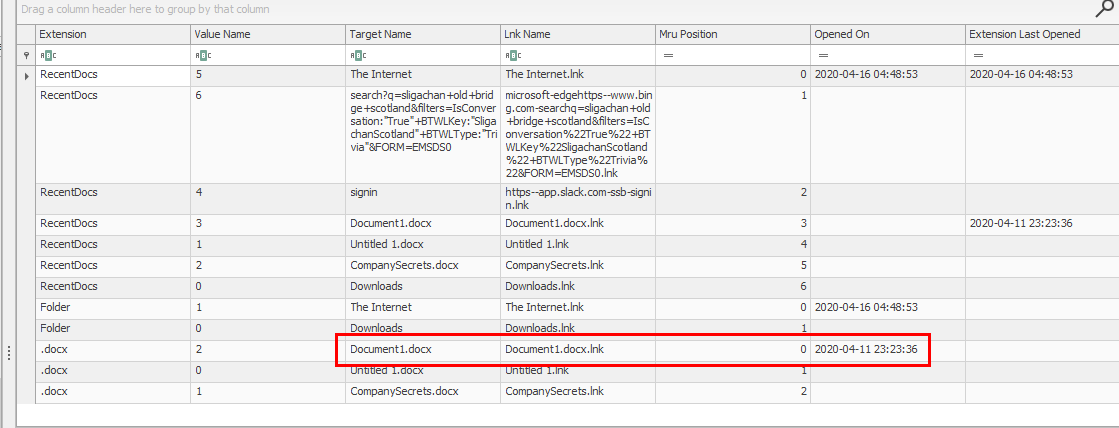
on the other hand, Jim opened 1 docx file
while Tim and Miriam didn't open any docx file neither
So we can use timestamp from Document1.docx that was opened by Jim to answer this question
2020-04-11 23:23:36
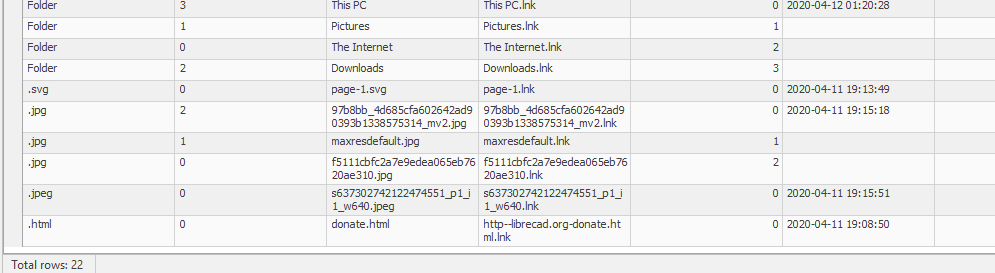
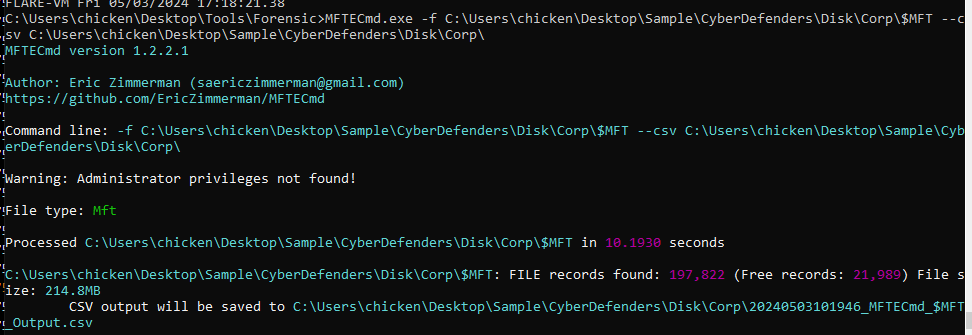
Q26: How many entries does the MFT of the filesystem have?
To solve this question, we need to use mftdump.exe which can be downloaded from
https://web.archive.org/web/20190705161925/http://malware-hunters.net/all-downloads
Its archive url from wayback machine because site was downed at the time I went to download this file But don't worry, We can still download this tool via Archive url
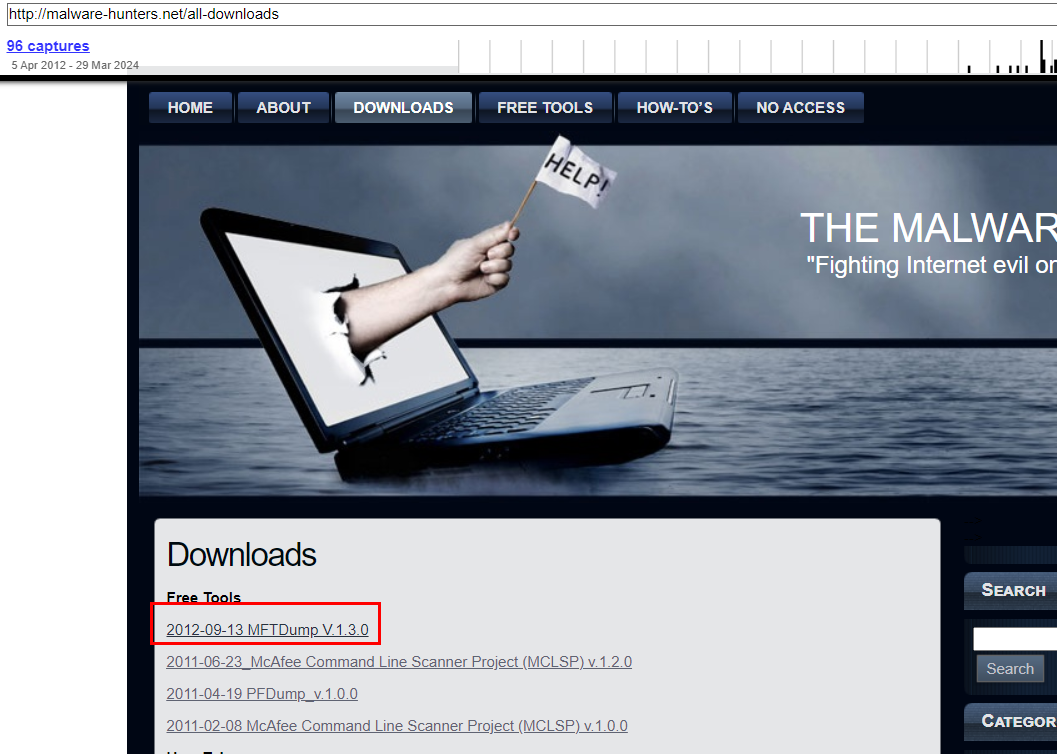
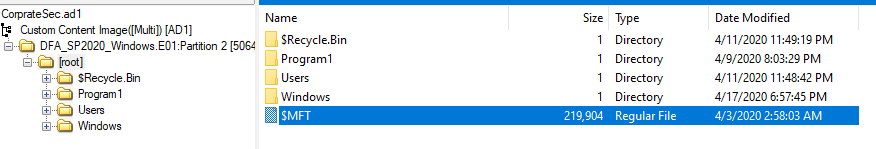
Export $MFT from root folder
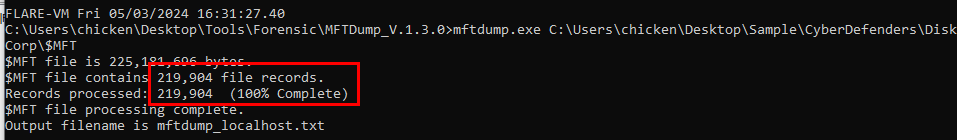
Use it to parse Master File Record file directly (mftdump.exe $MFT) and while processing it will tell us how many file records on this MFT file
219904
Q27: Tim wanted to fire an employee because they were ......?(Be careful what you wish for)
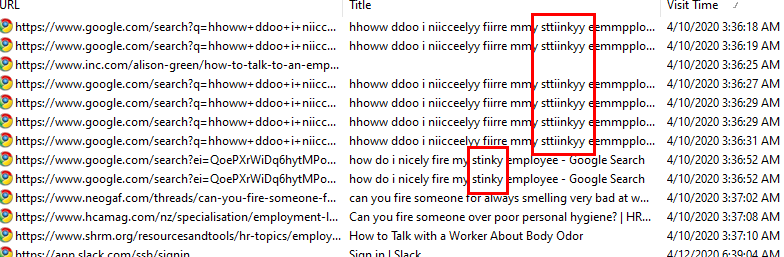
In question 15, we know that he wanted to kick out stinky employee based on his browser history
stinky
Q28: What cloud service was a Startup item for the user admin?
Grab admin's NTUSER.DAT hive then go to SOFTWARE\Microsoft\Windows\CurrentVersion\Run key
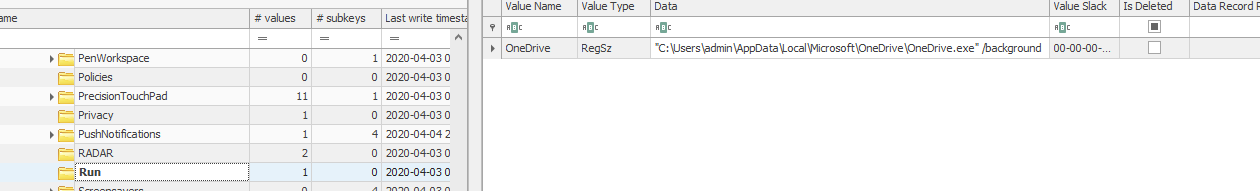
Only 1 service was stored in this key which is OneDrive, a cloud service from Microsoft
OneDrive
Q29: Which Firefox prefetch file has the most runtimes? (Flag format is
)
Export Prefetch folder then use PECmd from EZ tools to parse all Prefetch files
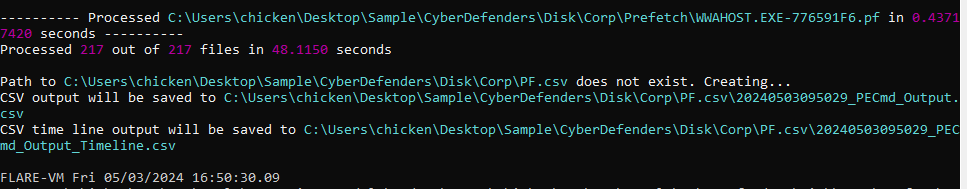
Use this command PECmd.exe -d Prefetch --csv pf.csv to process Prefetch folder and files then we got 2 csv files inside a folder we provided on this command
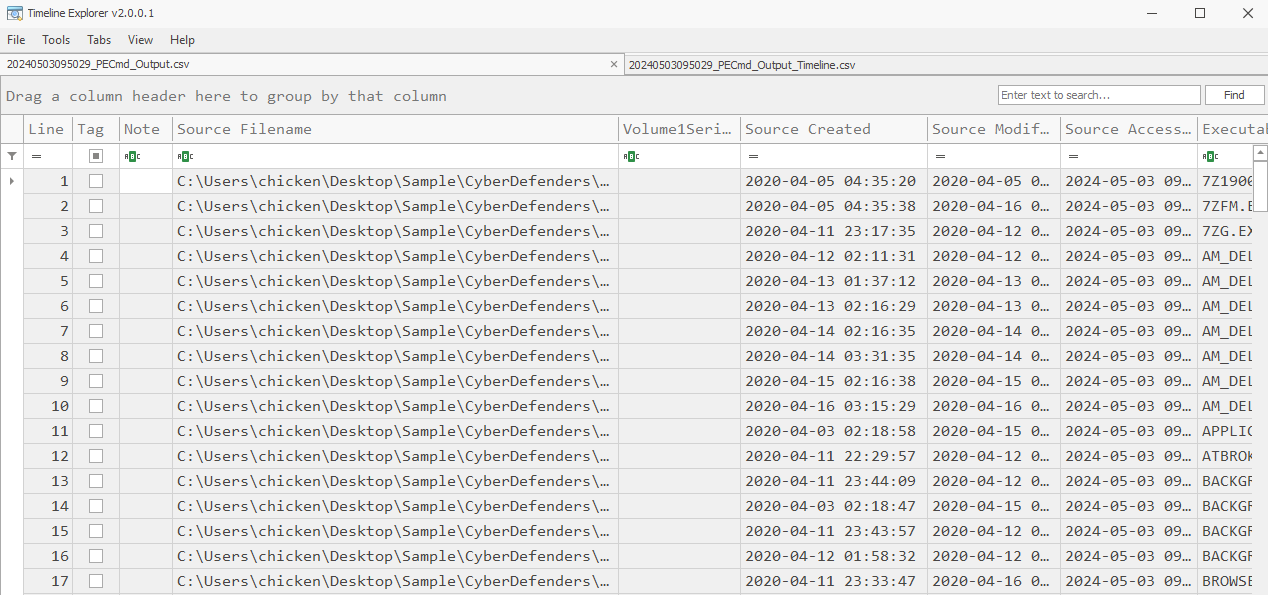
Ignore Timeline file but open the larger file on Timeline Explorer
We can see that this firefox prefetch file has the most run count among it peers
FIREFOX.EXE-A606B53C.pf/21
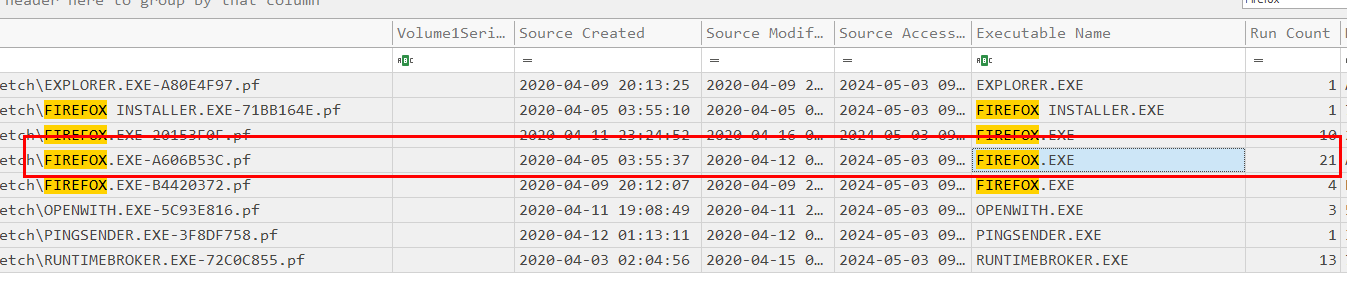
Q30: What was the last IP address the machine was connected to?
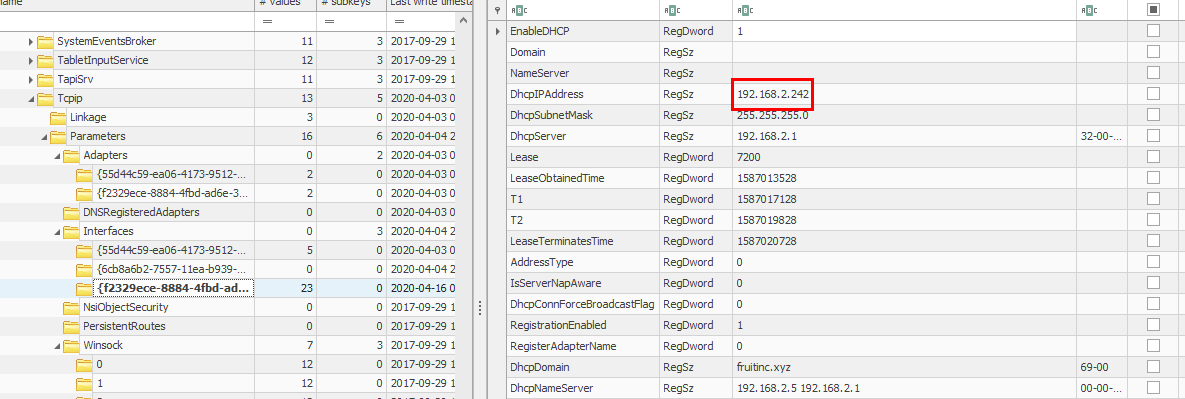
I was going to go to Event Log to search for this but I decided to take a hint and it tell me to go back to this registry key SYSTEM\ControlSet001\Services\Tcpip\Parameter\Interfaces
An answer of this question is the Dhcp IP Address
Which doesn't make sense to me at all, to be honest if we're really want to know the last IP address we should dig into Event Log but it is what it is
192.168.2.242
Q31: Which user had the most items pinned to their taskbar?
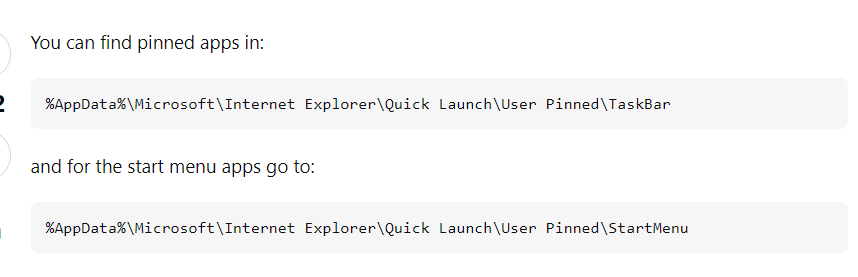
I did some research on this question about which registry key I should look at when it comes to taskbar and the most upvoted answer of this question tell me that I didn't need to dig into any register key, I just need to go to each user TaskBar folder which is located under AppData folder
Users\<username>\Appdata\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar
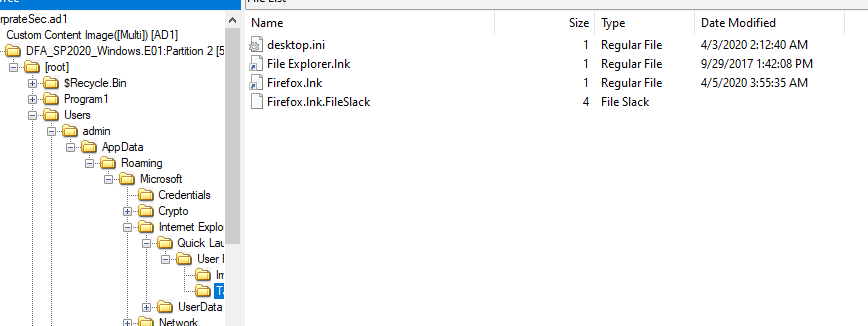 admin user has 2 shortcuts
admin user has 2 shortcuts
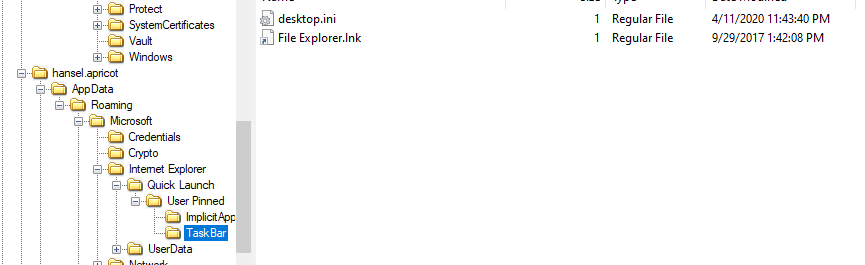
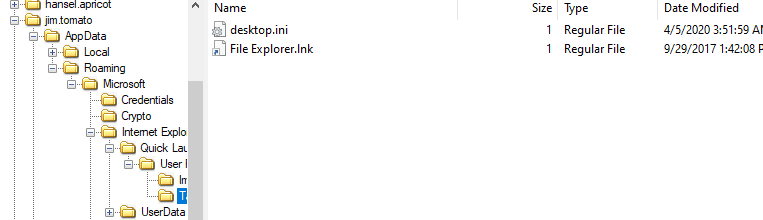
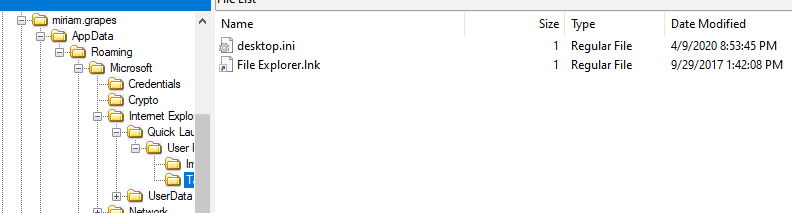
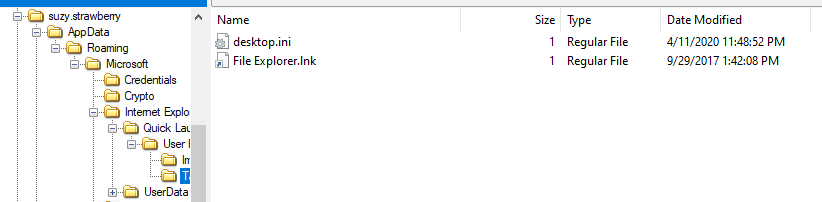
meanwhile all the rest have only 1 shortcut so admin pinned the most items to his taskbar
admin
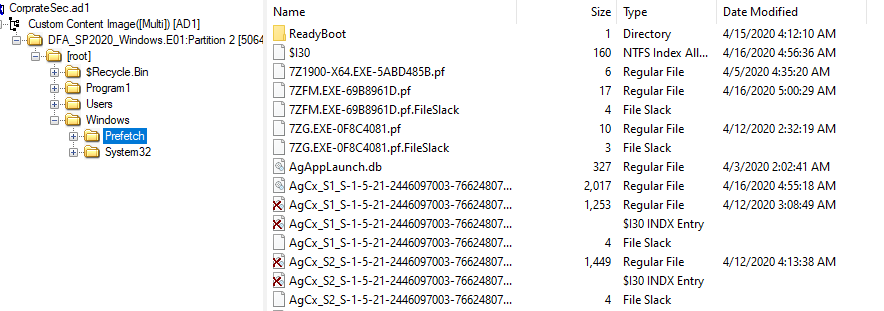
Q32: What was the last run date of the executable with an MFT record number of 164885? (Format: MM/DD/YYYY HH:MM:SS (UTC).)
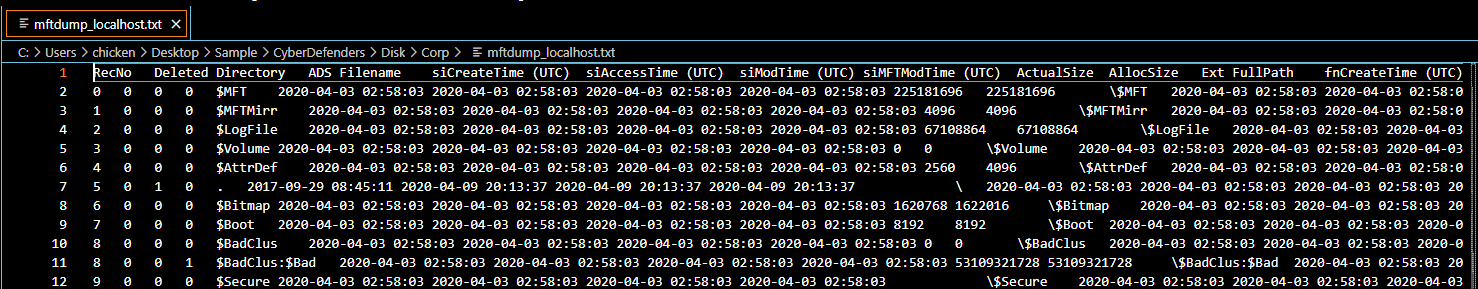
Using output file we got from mtfdump.exe to find which file has this record number
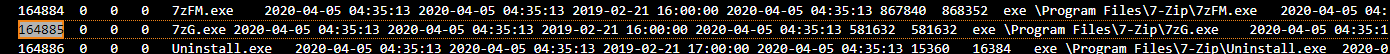
It's 7ZG.EXE
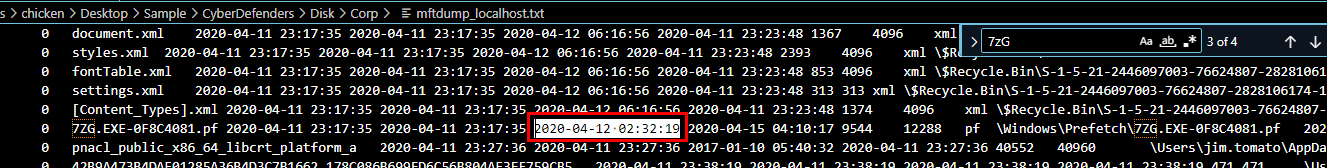
Find prefetch of this file then we got last run time
To verify this question we can use and output from PECmd
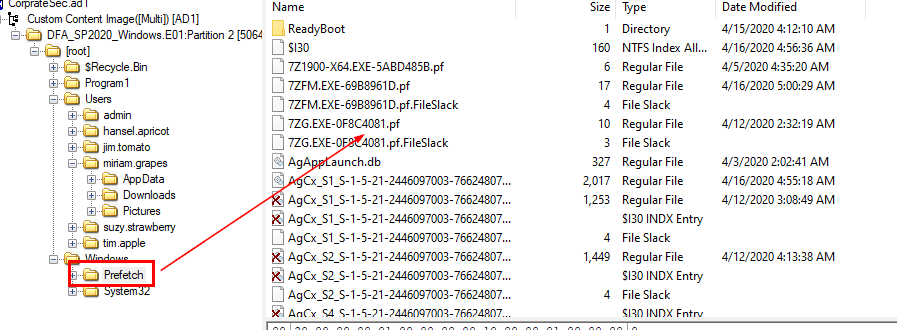
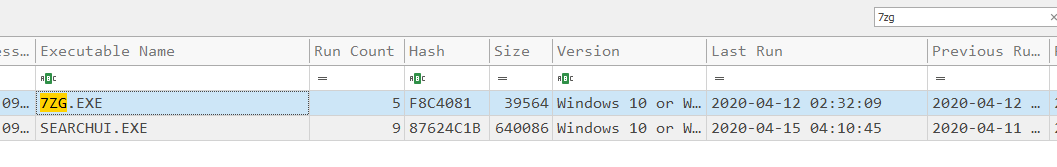
Well it's different from MFT output file but an answer of this question is the time we got from PECmd
04/12/2020 02:32:09
Q33: What is the log file sequence number for the file "fruit_Assortment.jpg"?
Output from MFTDump is not enough for this question, we need to use MFTCmd.exe from EZ tools
Parsing MFT using this command MFTECmd.exe -f $MFT --csv .
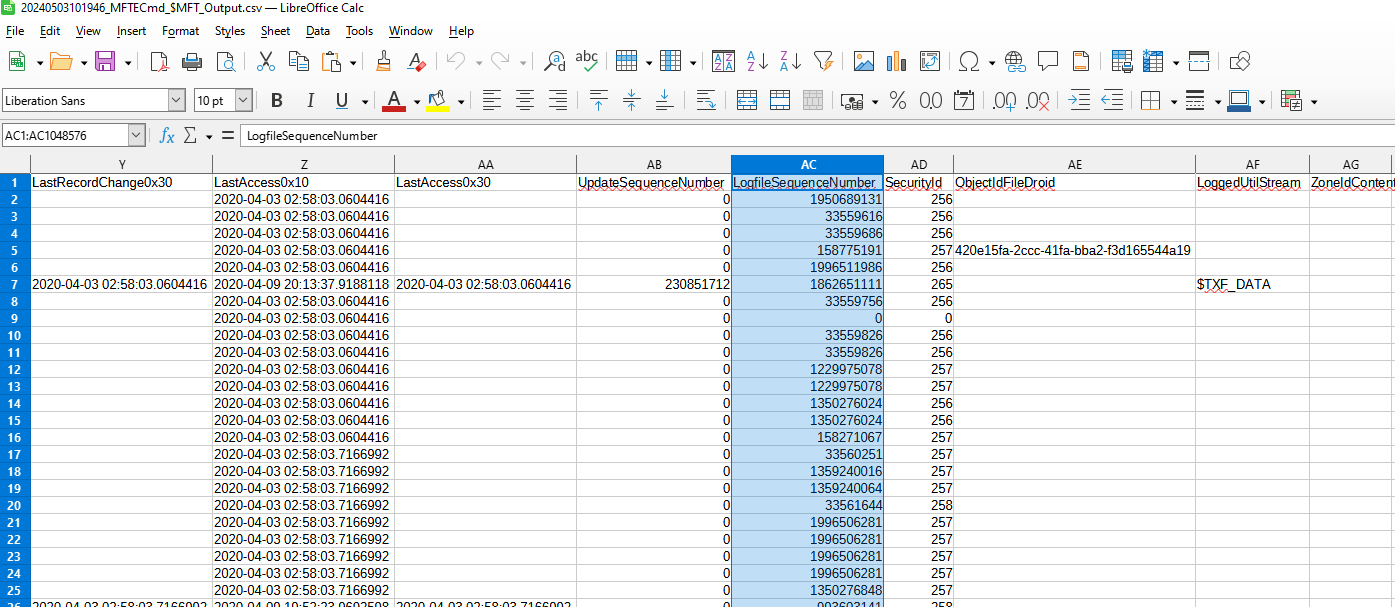
Open it with your CSV file viewer then we can see that there is LogfileSequenceNumber column which is the one we're looking for
Using search function to find for this image file and look up for LogfileSequenceNumber column
1276820064
Q34: Jim has some dirt on the company stored in a docx file. Find it, the flag is the fourth secret, in the format of <"The flag is a sentence you put in quotes">. (Secrets, secrets are no fun)
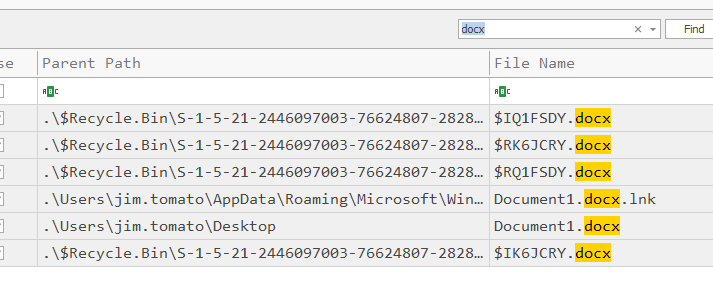
Using output from MFTECmd, we can search for docx file on Timeline Explorer directly which you can see that there is 1 docx file located inside Jim's Desktop
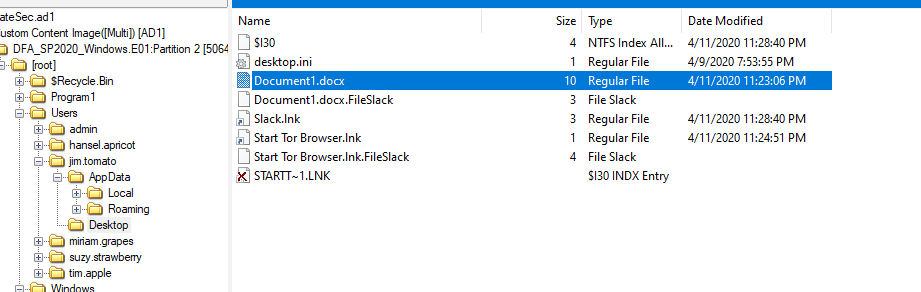
Go export this file
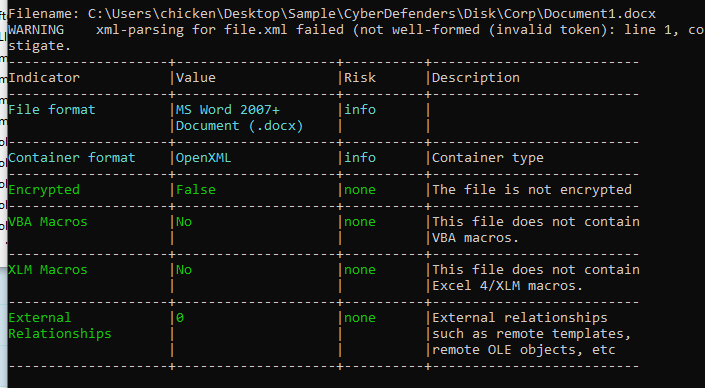
For safety sake, I used oleid from oletools suite to check if there is any suspicious indicator on this file (python oleid.py Document1.docx)
After confirming there is no suspicicious indicator, I opened docx file using LibreOffice which I found this message
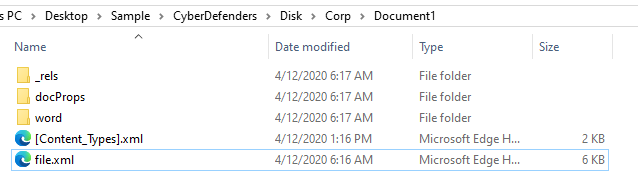
So I extracted docx file using 7z and file.xml caught my eyes immediately because it would have some message inside of it
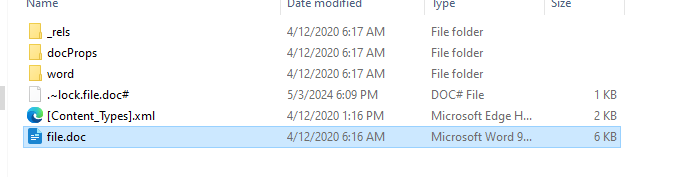
change file extension to doc and open it with LibreOffice again
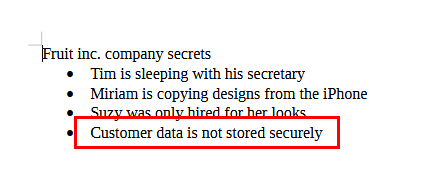
Then we finally see 4 company secrets
Customer data is not stored securely
Q35: In the company Slack, what is threatened to be deactivated if the user gets their email deactivated?
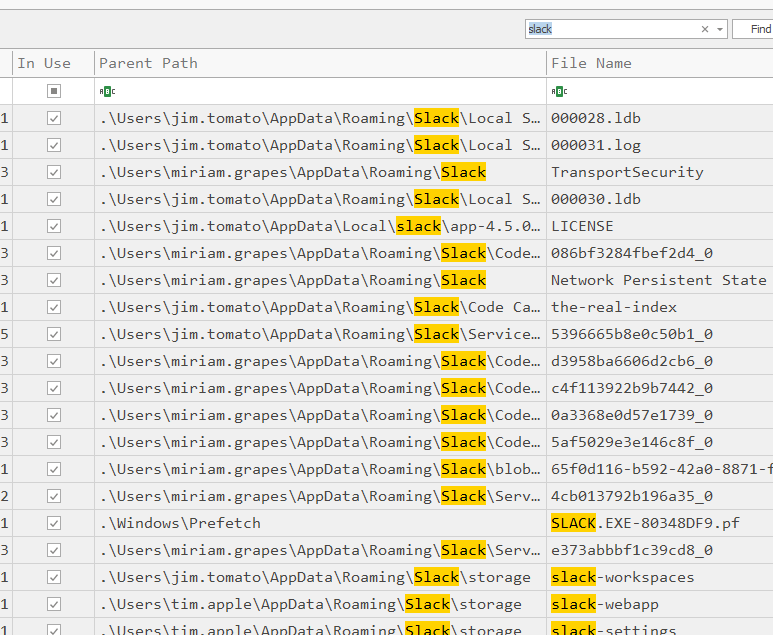
Searching for slack artifact using Timeline Explorer with an output from MFTECmd, we can see there is 1 log file located under jim's AppData
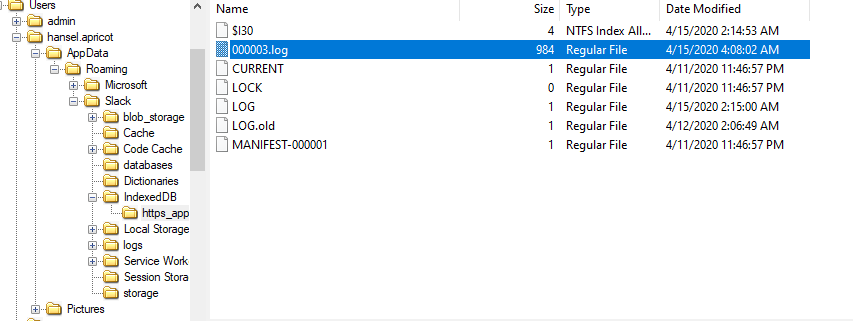
Grab it
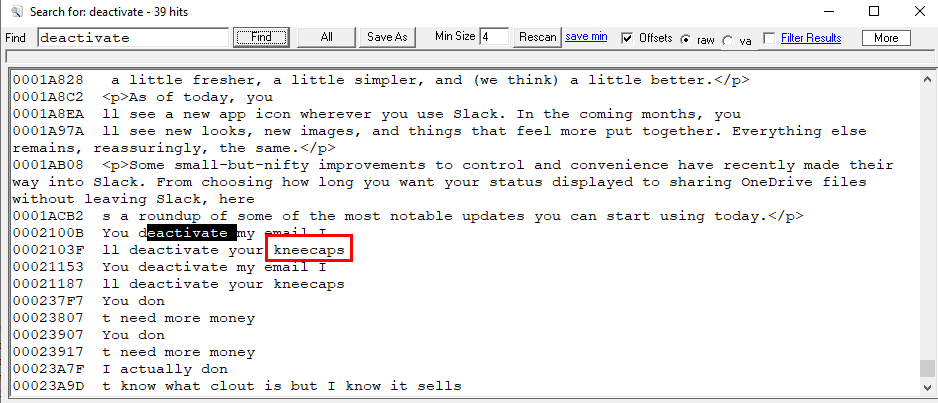
Using strings and searching for "deactivate", we found a message that if someone deactivate his email then he will deactivate kneecaps of that guy
kneecaps
https://cyberdefenders.org/blueteam-ctf-challenges/achievements/Chicken_0248/corporatesecrets/